
To convey language, the computing industry relies on American Standard Code for Information Interchange (ASCII), or 7-bit binary numbers used to depict every letter, number, and special character. ASCII doesn't allow for the straightforward representation of Unicode, or all the characters and symbols which factor into the computing industry's unified standard for coding and representing text. As a result, the industry turns to Punycode to get the job done. It's a way for using ASCII characters to represent Unicode. For example, Punycode turns "München" (the German name for Munich) into "Mnchen-3ya." Punycode is useful in that it allows domain registrars to register domain names that otherwise wouldn't cohere with the ASCII character set of the web's Domain Name System (DNS). But like most other technologies, this mode of representation is dual-use. Actors may use it for good, such as registering a legitimate site with München in its domain name. Or they may use it for bad. One of the most common ways to abuse Punycode is to conduct typosquatting attacks. These are campaigns by which attackers trick users into clicking on a link that contains Punycode because the domain name looks like one that's familiar to them. ɢoogle.com may look like Google.com, for example, but only the latter links back to the well-known search engine. The other redirects to a malicious website. Not all Punycode-based attacks are designed to trick users, however. Some are built to evade the protection systems that otherwise help protect users. Avanan’s cloud security researchers came across one such campaign in December 2016.
Looping Around Phishing Filters
The campaign detected by Avanan is different in that it fools Microsoft's Office 365 default phishing filters and tries to steal their Office 365 credentials. This attack begins with a fake FedEx email. Included in the email is a seemingly benign link for tracking a package that redirects to a malicious website.
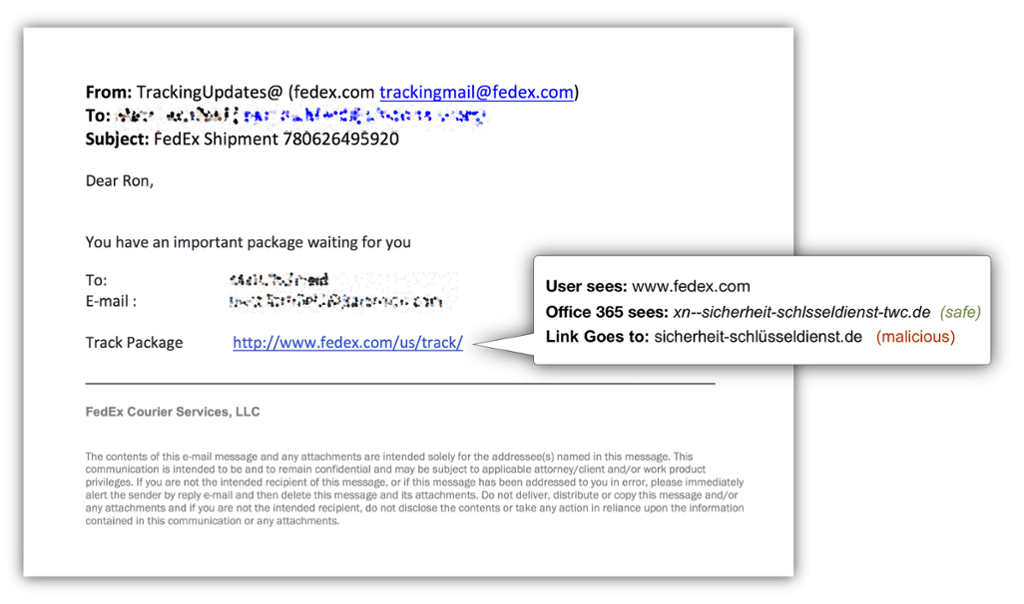
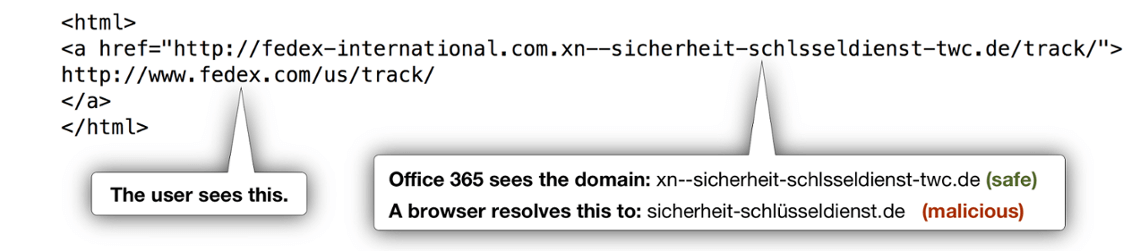
Sounds common, right? Not so fast! On the one hand, Microsoft's Office 365 analyzes the Punycode link in its ASCII format and not surprisingly confirms it as a safe site. But when the link resolves into its Unicode form, it points to a malicious location.
Avanan explains in its blog post:
" When testing the domain xn--sicherheit-schlsseldienst-twc.de as plain ASCII, it resolves to IP address: 81.169.145.66 (located in Berlin, Germany) that does not reveal any malicious intent. Therefore, the email is allowed through to the users’ inboxes. "But when a user clicks on the link, the browser translates the address to its Unicode format: sicherheit-schlüsseldienst.de that points to a different IP address: 92.242.140.21 (located in Belfast, Northern Ireland) …."
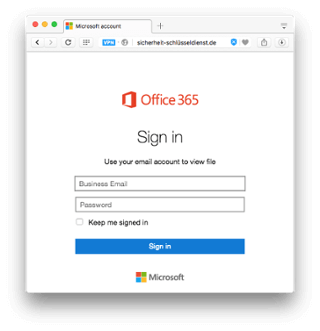
Located at that IP address is a fake Microsoft login page that asks users to enter their credentials for their "Business Email" account.
Conclusion
The use of Punycode makes this campaign different than other email-based attacks. Even so, it's still a phishing scam. That means users can protect themselves by not clicking on suspicious links, including a FedEx URL that redirects to an unfamiliar location. When a suspect URL comes their way, users should hover over it to determine if it leads to where it says it does.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

