
Researchers observed the distribution of the DanaBot banking trojan in a large attack campaign targeting U.S. organizations. On 26 September, Proofpoint detected a campaign consisting of hundreds of thousands of emails intended for U.S. recipients. Each of these attack messages masqueraded as an eFax and used a "Download Fax" link to download a document containing malicious macros. If enabled, those macros executed an embedded version of Hancitor, a threat commonly spread by phishing emails including some which posed as fake Delta Air Lines receipts. Hancitor then installed two versions of Pony stealer and DanaBot onto the infected machine.
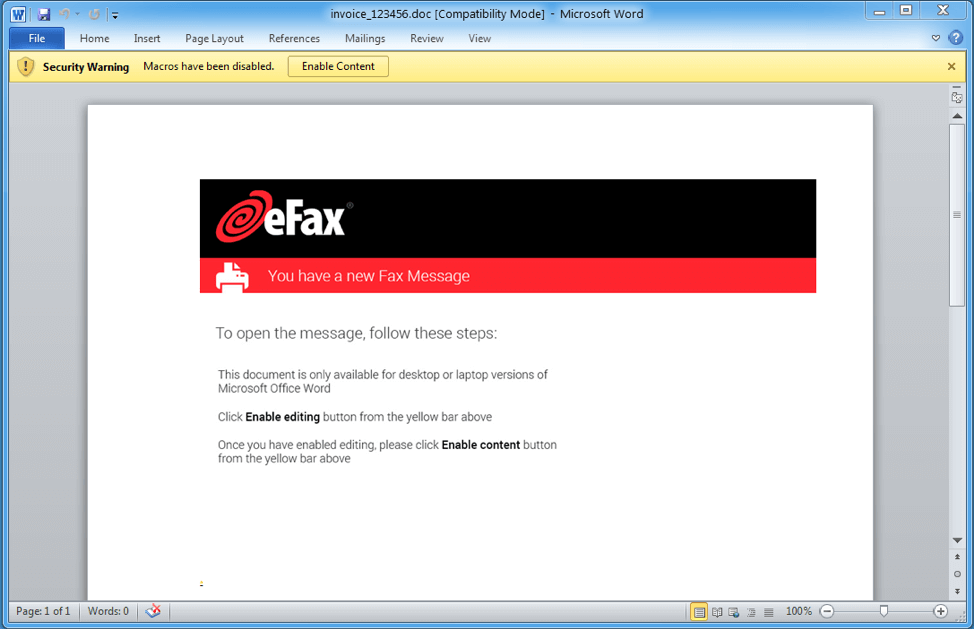
Malicious Microsoft Word document that contains the Hancitor payload. (Source: Proofpoint) Written in the Delphi programming language, DanaBot is a banking trojan that consists of three components. The DanaBot loader is responsible for executing the main component, which in turn configures and loads modules equipped with various malware functions. The threat also contains measures designed to prevent reverse-engineering. These features include the addition of extra conditions and loops to its code along with the employment of Windows API function hashing and encrypted strings that prevent automated tools from discovering DanaBot's true purpose. Proofpoint discovered DanaBot in May of 2018 when it observed a single actor using the threat to target Australian organizations. Over the next few months, the banking trojan began targeting companies located in a wide number of countries including Poland, Italy, Germany and Austria, as detected by ESET researchers. It continued to prey on targets in Australia during that time, also. Proofpoint's staff explained that DanaBot's inclusion in phishing emails targeting U.S. organizations means the malware isn't as geo-targeted as it once was. As quoted in a blog post:
Adoption by high-volume actors, though, as we saw in the US campaign, suggests active development, geographic expansion, and ongoing threat actor interest in the malware. The malware itself contains a number of anti-analysis features, as well as updated stealer and remote control modules, further increasing its attractiveness and utility to threat actors.
Responding to this growing interest among digital attackers, Proofpoint provided a number of indicators of compromise in its blog post that security professionals can use to block additional campaigns involving DanaBot.

