
Imperva has published some pretty interesting research on how an attacker might use cloud-based file synchronization services to exfiltrate data and deliver malware to systems inside an organization. The TL;DR of this attack is that a malicious adversary can steal and replace the authentication token for these services, allowing them to effectively both retrieve and plant files on the target system. They can then do all the bad things. They call the code that does this 'Switcher.' There were two sentences from this research document that jumped out at me as I was reading:
“The Switcher’s code is very simple. It does not interact with the Internet and does not rely on use of exploits. It only modifies some specific files or registry keys.”
And
“Once the Switcher’s code is done running, it can be removed from the endpoint, leaving no remaining traces of evidence of the compromise”
These two sentences caught my attention because Tripwire Enterprise can help in both of these situations. Monitoring systems for change is at the core of the product, including both files and registry entries. Monitoring in real-time is what allows us to capture changes, even if an attacker cleans up afterwards. While Imperva concluded that "this type of compromise is very hard to detect," I have to beg to differ--just a little.
Implementing MITC Monitoring with Tripwire Products
The key here is to identify the applications and dynamically apply monitoring policies to detect this type of activity. I'll describe how all of the Tripwire products can fit into this solution, but you, kind reader, can imagine how you might accomplish different parts of this task with individual products.
- Comprehensively inventory your environment for cloud-based file synchronization applications.
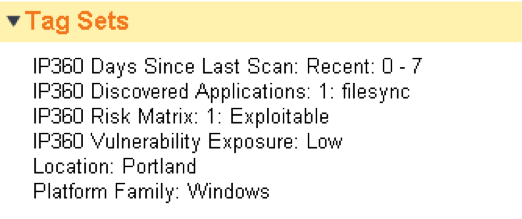
Tripwire IP360 can scan for and identify file synchronization applications like Dropbox and Google Drive. Once you've scanned, you can create reports filtered to show just these applications, but the step towards monitoring requires that you tag assets in Tripwire Enterprise where these applications exist. This is accomplished through the asset tagging integration between IP360 and Tripwire Enterprise. Let's say our tag is called 'filesync' in this case.
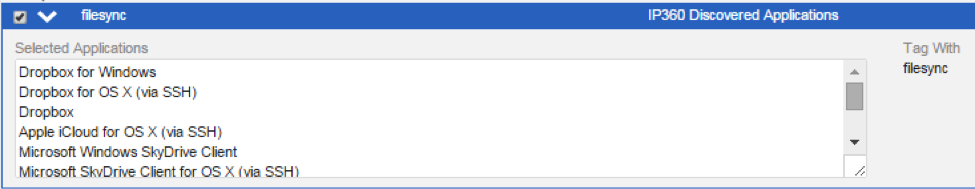
With this tagging rule created, IP360 will automatically tag assets in Tripwire Enterprise on which it finds any of these applications with the ‘filesync’ string. It will also keep that information up to date, removing the tag if those applications are removed.
Next, you can configure Tripwire Enterprise.
- Create and apply Tripwire Enterprise rules for the registry keys and files for changes and enable real time monitoring. The Imperva document outlines what needs to be monitored.
| Application | Registry | File |
| Google Drive | HKCU/Software/Google/Drive | OAuthToken_* | sync_config.db |
| Dropbox | config.dbx or config.db | |
| OneDrive | Windows Credential Store %USERNAME%\AppData\Local\Microsoft\OneDrive\ settings\Personal\user-id.txt | |
| Box | C:\ Users\%USERNAME%\AppData\Local\Box Sync\wincrypto_pass.cfg |
While it may be painfully obvious, it’s worth having Tripwire Enterprise watch for new files called ‘Switcher’ just in case. It’s possible to watch for a much broader range of new files as well, but it might be noisy, depending on how the system is utilized. Once the initial baseline state of the system is created, the Tripwire Enterprise agent can monitor for additions, modifications and deletions to these or any other files in real time providing a level of detection not found anywhere else and addresses the issue of the attacker trying to “clean up” after themselves. The policies created in Tripwire Enterprise don’t need to be applied across every asset in the environment. The tags created by IP360, along with any other context added through tags, can be used to dynamically apply monitoring policies. If an asset is running Dropbox, apply the right policy. If Dropbox is uninstalled, stop monitoring for these changes. Additionally Tripwire Enterprise’s ability to collect SHA-1 or other bits of data that make up an Indicator of Compromise allow the solution to integrate with an internal or external threat database. That is, when a change is detected the data is shipped to an IOC database to see if there is a match to any known (or potentially unknown) threats. If a match is found then alerts can be sounded and the troops rallied. This integration isn’t directly related to the Man-in-the-Cloud attack, but you could monitor synchronization folders for malware to detect the potential results of this type of attack. While Tripwire Enterprise itself has a host of options for reporting, alerting and taking automated action, there’s a final step if you want to correlate these events with other data.
- Alert on suspicious correlated events with Tripwire Log Center
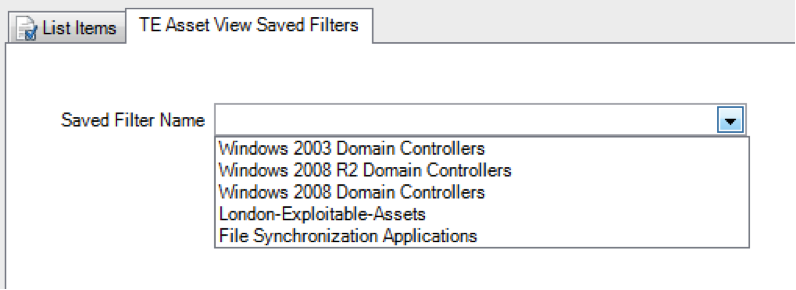
Change by itself isn't necessarily a problem, but sometimes a change is far more suspicious when correlated with other events and data. For example, if there’s exploit activity targeted at a host that has a file synchronization application on it, that might be worth an alert. To accomplish this correlation, you can send Tripwire Enterprise change data to Tripwire Log Center (or pretty much any logging/SIEM tool but TE integrates really well with Tripwire Log Center). With Tripwire Enterprise and Tripwire Log Center specifically, you can use the feature called Dynamic Correlation Lists. In Tripwire Enterprise, you start by creating a saved search for assets with the 'filesync' tag (or whatever combination of tags you want).

These saved searches will automatically show up as a dynamic correlation lists in Tripwire Log Center. That means that you can build correlation rules that use that dynamic list of assets. The end result is that you can create rules that dynamically correlate on the list of assets produced by those IP360 scans we set up at the beginning of this blog post.
Conclusion
Here’s what the product interaction looks like from a high level.

Ultimately, Tripwire Enterprise, integrated with our own or other solutions, can provide a high level of detection capability for compromises that other tools claim are “hard to detect.” While you can get valuable parts of these capabilities from individual products, I’ve told a story here that brings discovered data from vulnerability scanning, through to dynamically monitoring the environments, and finally to alerting and actions from correlated data. The Man-in-the-Cloud attack is one use case, but there are many others. This post benefited from the contributions of two other State of Security authors: Alex Cox and Chris Orr. They deserve a virtual high five for the help. Title image courtesy of ShutterStock

