
One of the best friends a user can have in today's digital age is a virtual private network (VPN). This tool masks a user's IP address and tunnels their data through a network of servers. In so doing, a VPN helps a user anonymously and more securely browse the web. Unfortunately, not all VPNs fulfill that purpose. A group of researchers from Queen Mary University of London and the University of Rome demonstrated as much back in January 2015. After examining 14 different services, the researchers found that 10 VPNs were susceptible to leaking IPv6 data and all but one were vulnerable to DNS hijacking attacks. Other groups have studied VPNs since then. Most recently, a team consisting of researchers from the University of New South Wales, the University of Berkeley, and Commonwealth Scientific and Industrial Research Organization (CSIRO) analyzed Android-based VPN apps. Their analysis demonstrated that dozens upon dozens of VPNs not only failed to uphold mobile users' privacy but jeopardized their security as well.
Exposed and Vulnerable: A Common Thread among Android VPN Users
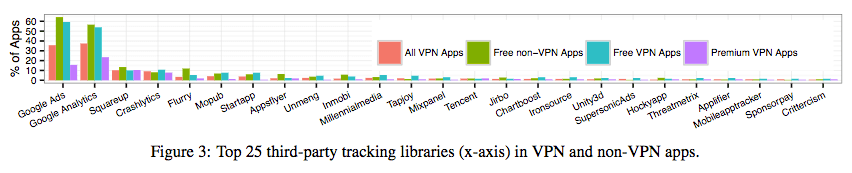
For their study (PDF), the researchers searched on Google's Play Store for VPN-related apps. They identified a total of 1,488,811 free and paid potential candidates. Next, they obtained each app's metadata, downloaded the app's executable, and analyzed its source code and AndroidManifest file. This file is crucial. App users leverage it to request either custom VPN permissions or BIND_VPN_SERVICE, Android's official VPN permission which exposes an app to and routes all a device's traffic through a virtual network of servers. Overall, the team identified 283 free Android apps that requested the VPN permission in their AndroidManifest files. Many of those apps exhibited some startling behavior that jeopardized users' privacy and security. Here's a sampling of what the researchers found: Lack of Encryption Nearly one-fifth (18 percent) of the apps didn't use encryption with their tunneling protocols. When coupled with the fact that 84 percent and 66 percent of the apps didn't tunnel IPv6 and DNS traffic respectively, it becomes clear that many Android VPNs failed to achieve security and anonymity for their users. If anything, they lowered the difficulty of government agents and others abusing those apps to track users' online movements. Trackers 67 percent of the free apps analyzed embedded at least one third-party tracking library in the source code. To a certain extent, these apps relied on advertising and revenue generated from analytics services for funding. By comparison, 65 percent of premium (paid) VPNs apps didn't come with at least one embedded tracking library at the time of the study.
Malware Close to one in 10 (eight percent) of the VPN apps contained at least one positive malware report from VirusTotal. Nearly half (43 percent) of those reports resulted from adware. The rest came from trojans (29 percent), malvertising (17 percent), riskware (6 percent) and spyware (5 percent). Injecting JavaScript Code Two free VPN apps (VPN Services HotspotShield by AnchorFree and WiFi Protector VPN) actively injected JavaScript code using iframes to track users and display their own advertisements. Were an attacker to compromise either of these two apps, they could exploit this functionality to load malicious iframes and infect users with malware. Actors could also leverage malicious iframes to conduct social engineering attacks that seek to steal users' login credentials for various web services.
Conclusion
Most if not all the VPN apps analyzed by the researchers claim they're designed to uphold users' anonymity and security. Yet this research project illustrates many of those apps failed in that endeavor. In some cases, they exposed users to additional risk. Following the conclusion of their study, the researchers shared their findings with several of the VPN app developers. Some made an effort to fix the issues affecting their creations. Dali Kaafar, professor and senior principal researcher in online privacy and security at CSIRO, explains in a blog post:
"Several of them [app developers] took actions to fix the identified vulnerabilities. Some apps were even removed from the Google Play Store."
This study illustrates how users need to be careful when installing VPN apps. They should read reviews of an app they're considering downloading. Additionally, they should never download an app from outside the Google Play Store, especially a suspicious mobile VPN service that requests an unnecessary amount of permissions.

