
Researchers observed that the Emotet gang had incorporated a new "Red Dawn" template into their weaponized Word Documents delivered to users. Until recently, Emotet's handlers had been targeting users with a iOS-themed document template for their malicious Word documents. The template explained that a sender had created the document on iOS, and it informed the recipient that they needed to click the "Enable Content" button in order to properly view the document's contents. Documents employing this template arrived as attachments that came disguised as invoices, COVID-19 information and resumes in the group's ongoing spam email attack campaigns. That changed later on in the summer, however, when Emotet expert Joseph Roosen came across a new template that he named "Red Dawn" as a result of its red accent colors. Per Bleeping Computer's reporting:
The Red Dawn template also moves away from its iOS theme and now states that "This document is protected" and that previewing is not available. It then prompts the user to click on 'Enable Editing' and 'Enable Content' to view the document.
As with the previous template, the Red Dawn template used malicious macros to install Emotet on the recipient's computer.
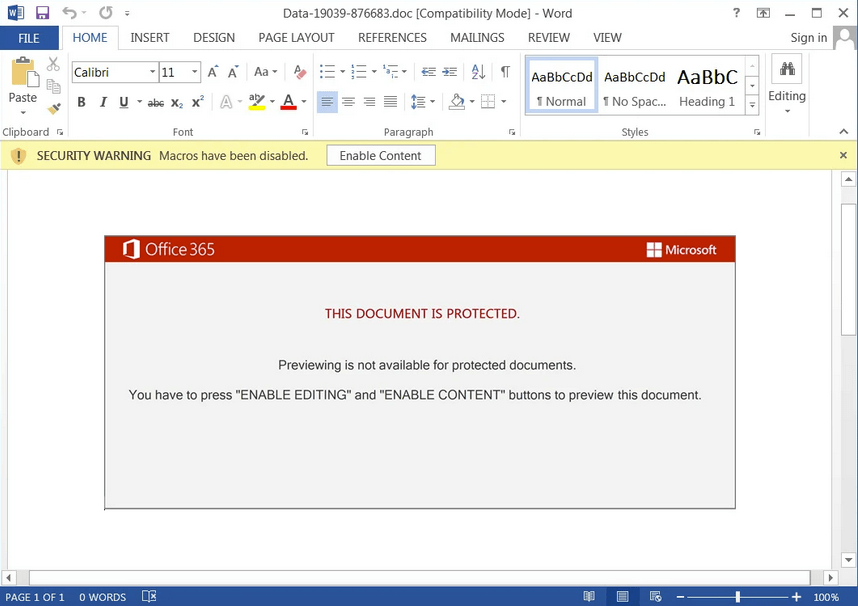
A screenshot of a malicious Word document using the Red Dawn template. (Source: Bleeping Computer) At that point, attackers could have used Emotet to install additional threats such as TrickBot or QBot onto the infected machine. Those malware families might have then dropped their own payloads including samples of the Conti or ProLock ransomware families. News of this change in templates follows just weeks after the Emotet botnet earned the title of “most wanted” malware family for the month of July 2020 following a five-month period of inactivity. The commitment of Emotet gang to update its creation on an ongoing basis highlights the need for organizations to protect themselves against malware infections. They should specifically have the ability to examine suspicious files in a quarantined environment while gaining important context into system changes. Learn how Tripwire File Analyzer can help.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

