
It's no secret attackers used insufficient IoT security to their advantage in 2016. Who can forget October 21? On that day, multiple distributed denial-of-service (DDoS) attacks struck the internet performance management company Dyn, a multi-pronged offensive which caused Etsy, Spotify, Twitter and other large web services to suffer connectivity issues and service interruptions. The security community later found out that Mirai and other malware conducted those attacks using a botnet of routers, IP cameras, and other Internet of Things devices. Mirai created its botnet by exploiting a common security problem among IoT devices: preconfigured administrator passwords that are oftentimes available online. The malware leveraged these credentials to enslave devices and enlist them into its ranks. Unfortunately, ready access to device login credentials is just the beginning of the Internet of Things' security woes. Many device manufacturers release firmware updates infrequently or not at all, whereas other devices come preprogrammed with their telnet and/or SSH ports open to the outside world. These security shortcomings considered, it's not surprising that attackers go after web-connected IoT devices, try to assume control over them and abuse them for nefarious acts if their hacks prove successful. Kaspersky Lab's Vladimir Kuskov, Mikhail Kuzin, Yaroslav Shmelev, Denis Makrushin, and Igor Grachev elaborate on what bad actors can do with a compromised "smart" product:
"The most common scenario is your device ending up as part of a botnet. This scenario is perhaps the most innocuous for its owner; the other scenarios are more dangerous. For example, your home network devices could be used to perform illegal activities, or a cybercriminal who has gained access to an IoT device could spy on and later blackmail its owner – we have already heard of such things happening. Ultimately, the infected device can be simply broken, though this is by no means the worst thing that can happen."
But the Kaspersky researchers wanted to learn more. They wanted to better understand the timing of an IoT-enabled attack. So they set up some honeypots imitating devices running Linux and waited. It turns out they didn't have to wait too long. As the researchers explain:
"… [A]fter just a few seconds we saw the first attempted connections to the open telnet port. Over a 24-hour period there were tens of thousands of attempted connections from unique IP addresses."
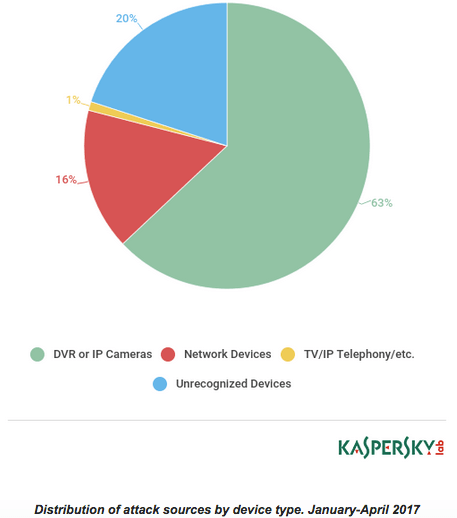
The attempted connections used the telnet protocol in most cases; the rest used SSH. Overall, more than half (63 percent) of the attack attempts originated from IP addresses linked to DVR services or IP cameras. One-fifth of the connections came from network devices and routers.
However, some of the origin IP addresses were a bit more alarming in that they linked to enterprise security solutions or industrial control systems (ICS). Connection attempts arrived from point-of-sale devices at restaurants and stores, for example. Others came from power management systems and even a monitoring system at a seismic station in Bangkok. Acknowledging the results of this experiment, it's important that users and businesses alike research IoT devices carefully before they purchase them. Ideally, they should choose a device that allows them to change the default password and that receives firmware updates on a regular basis. If they purchase a product that doesn't allow these security safeguards, users should disable all network services they don't use on the device and prevent web access outside of the local network.

