
If you read my previous post about Microsoft ending extended support for Windows Server 2003 (WS2003) on July 14, 2015, you’re familiar with what that means - Microsoft will not be providing further security patches, hot fixes, or software updates without a costly extended support agreement. “Many IT teams are very comfortable using Windows Server 2003 for a print or file server because it’s a very stable product, and they know how to patch and maintain it,” said Lane Thames, security researcher for Tripwire. “However, we should expect a new wave of exploits targeting all types of WS2003 systems by mid-August, and these attacks will target devices running critical business applications. Any organization that hasn’t completed the transition by July should a hardening plan into place immediately.” Top Concerns – Security and Compliance Top concerns for businesses facing this deadline are security, compliance, and vulnerability management for the 1.76 million – 2.8 million WS2003 systems that will not be migrated by the July deadline. Over one third of the respondents to the referenced survey were most concerned about their mission-critical applications - financial, ERP, and CRM. A Checklist of Practical Steps for Proactive Hardening of Your WS2003 Systems There are actually several practical steps you can take to proactively protect your WS2003 servers against a range of possible upcoming attacks:
1) Assure Patching is Up To Date
There are some who think hackers are actively compiling attacks to launch post-July 14, 2015. Much of this type of hype did not materialize for XP, but given that these are servers – a common target for attackers and often housing with attractive data – it could indeed be a serious concern. Therefore, getting up-to-date on available WS2003 patches is a requirement for any IT team supporting W2003 post-deadline. All the applications running on those servers should also be up-to-date with available patches. While you’re at it you should also assess if your WS2003 servers have unnecessary software or services on them – remove what you can to simplify and reduce the potential attack surface of those systems.
2) Create a “Vintage CVE Patch Collection”
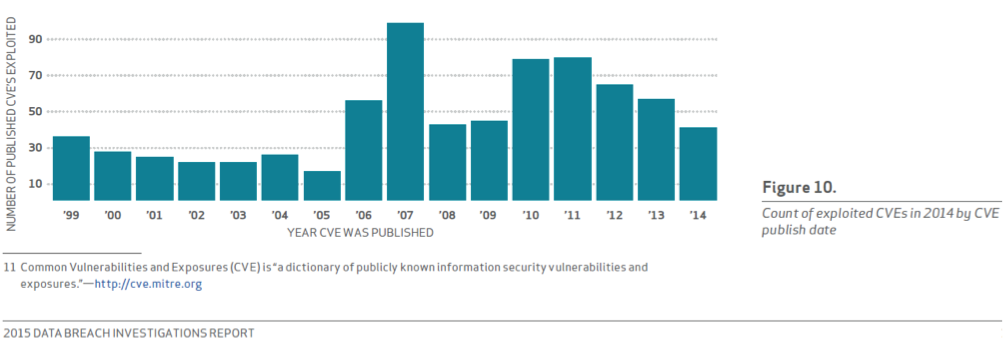
The chart below from the 2015 Verizon Data Breach Report (DBIR) shows the CVE publish date and counts of exploited CVEs in the breach data from 2014. Findings were that old exploits were still in use by attackers – dating as far back as 1999, even though patches were available. While this data is not specific to WS2003 OS vulnerabilities, it’s still a sobering analysis. The Verizon DBIR advice was to create that list of old CVEs and the corresponding patches and apply them. You can use this list if you need to reimage one of the WS2003 systems.
3) Important Patches
Tripwire has published a whitepaper with guidance for key CVEs, Java and Adobe vulnerabilities, and SSL and TLS vulnerabilities. In general, remote code execution, remote access software, weak encryption, and other poor security practices should be reduced or eliminated.
4) Check for Configuration Weaknesses
In many cases, just by utilizing foundational security controls, organizations can “harden” WS2003 servers against possible attack, insider threats, or unauthorized access through secure configuration management. Some Common WS2003 system configuration weaknesses are:
- Windows Remote Access software is enabled without configuring to only allow system administrator access
- All shares may not be configured to prevent anonymous access
- Anonymous access to Windows shares and named pipes is allowed
- Windows default guest account is enabled
- Strong encryption is not set for Windows network sessions on servers
- Windows password complexity is not enabled
- Windows network passwords are not forced to be encrypted
- Windows password length is not configured to be a minimum of 8 characters
- Windows account lockout is not configured for a minimum of 15 minutes before reset
- System event log is not configured to a sufficient size
- Logging for successful and failed logon attempts is not enabled (for domain accounts or local accounts)
5) Establish a Baseline and Harden Systems
Perhaps it goes without saying that having a backup of a known good state for your WS2003 devices is a good idea, particularly before July 14, 2015. One way to build a “known good” baseline is to install an agent that will quickly map the current configuration including all applications and their versions and patch levels, .exes, DLLs, ports, services, configuration files and settings, OS versions and patch levels, protocols in use (like SSL and TLS) as well as identify encryption strengths. This will expose potentially exploitable weaknesses in your systems, and it is critical because a high percentage of exploits take advantage of misconfigured or weak system configurations, or vintage vulnerabilities. Save your “known good” backup, and if something occurs in the future, you can recover quickly. Much of this is basic security hygiene. However, now is the time to evaluate your security practices and address any weaknesses that may have crept in over time. New WS2003 exploits and zero-day attacks will continue to surface, but you can make it as difficult as possible for your servers to be breached if you act now. The final third post in this series of three will be on reporting to the business leadership, C-suite, and boards of directors so that they are as informed as possible about the risks and the decisions of which they share a part. Looking ahead, all businesses should consider taking advantage of SecureCheq, a free tool that tests for common configuration errors and weaknesses in Windows Server 2003. Title image courtesy of ShutterStock
Tripwire ExpertOps
Elevate your organization's cybersecurity with Tripwire ExpertOps! Explore our managed security service now to ensure round-the-clock protection and expert guidance in safeguarding your digital assets.

