
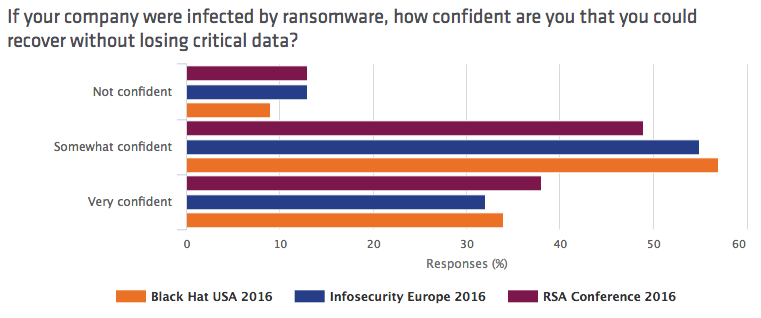
Ransomware is having quite the year. According to the FBI, crypto-malware authors extorted more than 200 million USD from users in the first three months of 2016. They're well on their way to raking in over one billion dollars by the end of the year. Part of the reason ransomware developers are doing so well, the FBI explains in a letter, is because they're attacking an increasing number of targets, including hospitals, state and local governments, law enforcement, and small businesses. Nearly 50 percent of organizations in the United States suffered a ransomware attack in the past 12 months alone, Malwarebytes found in a survey. That's not to say most victims paid the ransom. Three percent submitted a payment, a decision which cost 82 percent of affected organizations important business files. Crypto-malware attacks are also becoming more sophisticated. Recognizing a growing awareness of spam campaigns among users, computer criminals are turning to other means, such as spear-phishing (or whaling) emails and exploit kit attacks, that don’t require user interaction. As ransomware attacks increase in frequency and sophistication, information security professionals are apprehensive about their organizations’ abilities to protect themselves. For instance, in a survey of 200 security professionals who attended RSA Conference 2016, Tripwire found that only 38 percent of respondents said they were "very confident" they could recover from a ransomware attack without losing critical data. The advanced threat provider found a similar consensus among 400 IT personnel at Infosecurity Europe 2016: only 32 percent stated they could confidently recover from a crypto-malware infection without suffering data loss. To develop an even fuller picture of organizations' ransomware preparedness, Tripwire decided to ask the same questions of over 220 information security professionals who attended Black Hat USA 2016, one of The State of Security's top 11 infosec conferences. Overall, it found more of the same. When asked if their companies could recover from a ransomware infection without losing critical data, only 34 percent of the respondents said they were "very confident" they could do so. Nearly one in 10 professionals (nine percent) said they were not at all confident.
Travis Smith, senior security research engineer at Tripwire, feels these statistics could reflect a lack of preparedness among organizations:
"Successfully recovering from ransomware is well documented, whether through data recovery to paying ransom. It’s important for businesses to understand the costs associated with data recovery so that they’re prepared for a ransomware infection. Follow the 3-2-1 data backup rule: gather three copies of the data on two different types of media, with one of these copies stored off-site."
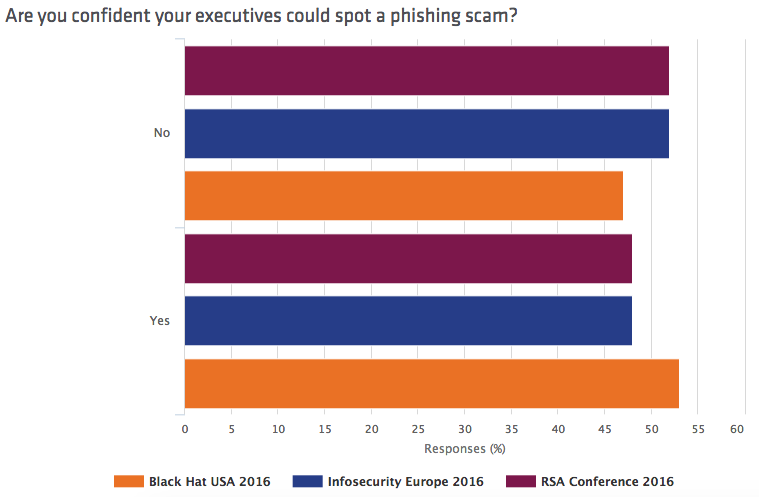
In addition, Tripwire found that only 19 percent of respondents considered ransomware one of two top threats faced by their organizations. Only a slightly higher fraction of participants (22 percent) said the same about phishing attacks, a common distribution vector of ransomware. That lack of concern ties into the fact that close to half (47 percent) of respondents said they weren't confident their executives could spot a phish.
Not all organizations are prepared for a ransomware attack. But as Travis rightly states, they can begin to strengthen their security posture by investing in employee security awareness training:
"Training is a vital aspect of preventing successful phishing attacks, especially as spear-phishing and 'whaling' campaigns can be more difficult to detect. It’s increasingly important for executives and high-profile employees to be prepared. Users should assume links and attachments are guilty until proven innocent; verify the sender’s intent before trusting their data."
To prepare employees, companies can circulate Tripwire's ransomware and phishing awareness videos among their workforce. They should then consider pursuing other ransomware prevention strategies. To learn more about ransomware, please click here.
