In the information age, an organization is nothing without its critical endpoints. Those network systems function as the cornerstones of a corporate IT network and, as such, are crucial to maintaining smooth business flow. Without them, a company could suffer fiscal and/or operational consequences. Critical endpoints come in many shapes and sizes. Traditionally, employees have relied on desktops, tablets and phones to do their jobs. But that's all changed with the Internet of Things (IoT). Nowadays, virtual machines, point-of-sale (POS) terminals and IoT devices dot companies' IT network environments. The proliferation of endpoints presents certain challenges, especially in industrial control system (ICS) environments where the Industrial Internet of Things (IIoT) is poised to create a number of new "smart" paradigms in energy, healthcare and other critical areas. More devices mean more risks against which security professionals must defend, and with Intel projecting there will be over 200 billion connected devices by 2020, IT personnel could very well have their work cut out for them in securing all of those new endpoints. To address the challenges of the IoT, many in the security community feel information technology and operational technology should converge and cooperate. Organizations could then leverage that union to develop an enhanced endpoint security strategy, they argue, one which would encompass all endpoints in the post-IoT world. But that's assuming companies already have a security strategy for the growing number of endpoints on their network. As it turns out, most enterprises don't. That's one of the major findings of Tripwire's 2016 security challenge survey on endpoint growth. For its study, Tripwire commissioned Dimensional Research to evaluate some of the major challenges organizations face when it comes to optimizing their information security and compliance programs. Dimensional Research asked 500 respondents about whether they have a security strategy to protect their organization's endpoints. Only a third said they had such a plan in place, while even more than that (40 percent) said they were not at all confident those endpoints receive security updates in a timely manner.
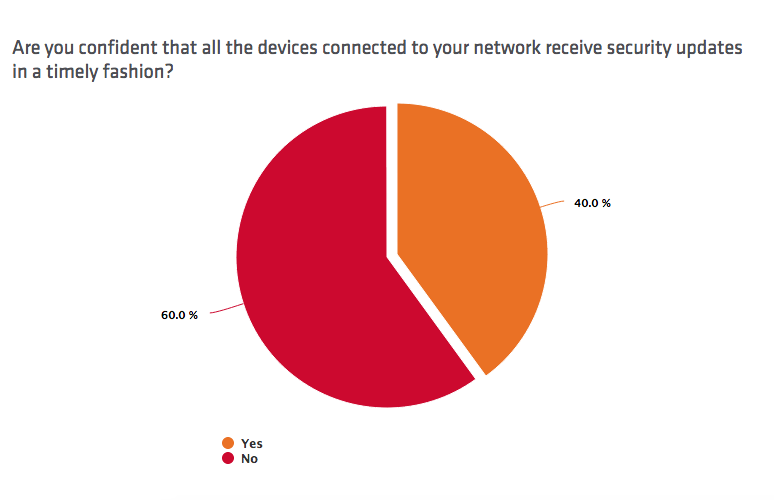
Untimely patches are a major concern for Tim Erlin, senior director of IT security and risk strategy for Tripwire:
"Timely application of security updates is one of the most effective ways to reduce risk in any organization, but it remains a widespread challenge. As more diverse devices are deployed, the availability and management of these updates becomes more difficult. Organizations need to have a strategy now, before an incident occurs."
Unfortunately, Dimensional Research also found that a minority of respondents are treating IoT as a serious concern to their organization's network security. Close to one-third (31 percent) of participants said they conduct inventories of their hardware- and software-based assets only once a year, while only 15 percent said they do so continuously. Additionally, only 21 percent respondents said they consider the IoT a top security concern for their organization. 10 percent reported they don't see the significance of the Internet of Things despite having installed various IoT devices on their network.
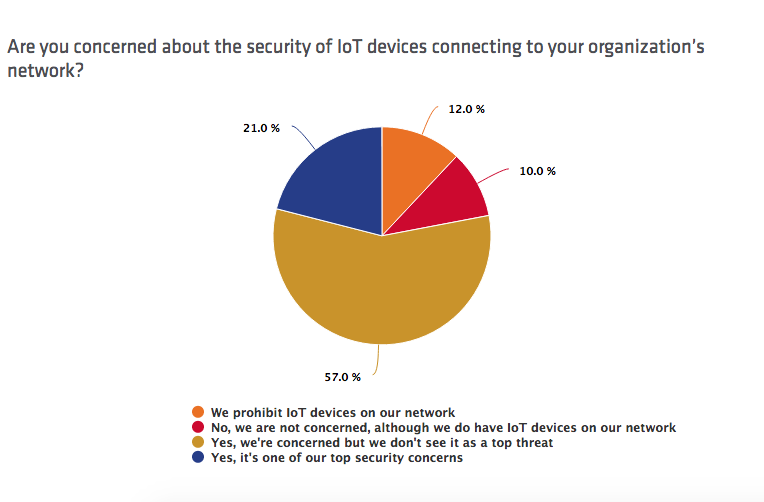
Dwayne Melancon, vice president of products at Tripwire, feels these mindsets are dangerous given industry estimations about the ongoing growth of IoT:
"The proliferation of devices from BYOD, IoT, and the incidental use of personal devices in the enterprise is causing 'device sprawl,' so it's no surprise enterprises aren't keeping up. The key to dealing with this risk is to remember that foundational controls still apply, regardless of scale – know what's on your network, understand how it’s vulnerable, keep it patched, keep it securely configured, and monitor the heck out of it for suspicious activity."
You can read more endpoint security tips by downloading Tripwire's free eBook Endpoint Detection and Response for Dummies. For more information on Tripwire's survey, please click here.
