
An ongoing spear-phishing campaign is using malicious Microsoft Word documents to install two PowerShell backdoors on victims' machines. FireEye as a Service (FaaS) first detected the operation in February 2017. The campaign appears to be targeting individuals who've played a part in submitting financial statements and other documents to the U.S. Securities and Exchange Commission (SEC). Sometimes, those documents mention participating individuals by name. Each attack email contains a spoofed sender email that uses the official SEC domain "sec.gov". The emails also come with an Microsoft Word attachment whose name indicates the SEC has updated Form 10-K, an annual report required by the U.S. Securities and Exchange Commission because it gives a comprehensive overview of a company's financial performance.
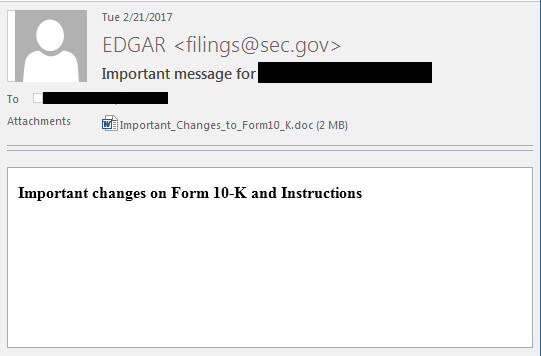
Example phishing email sent in the campaign. (Source: FireEye) Not surprisingly, the attachment isn't what it says it is. FireEye threat researchers
"The malicious documents drop a VBS script that installs a PowerShell backdoor, which uses DNS TXT records for its command and control. This backdoor appears to be a new malware family that FireEye iSIGHT Intelligence has dubbed POWERSOURCE. POWERSOURCE is a heavily obfuscated and modified version of the publicly available tool DNS_TXT_Pwnage. The backdoor uses DNS TXT requests for command and control and is installed in the registry or Alternate Data Streams."
POWERSOURCE is capable of doing many things. In some cases, it loads up a second-stage PowerShell backdoor to further infect the victim. Cisco Talos researchers have analyzed this activity in what appears to be a similar attack campaign. Other times, the campaign links to a domain hosting a Cobalt Strike Beacon payload. The domain also is known to host Carbanak malware, which isn't new to the threat landscape. So far, researchers have detected 11 organizations in financial services, transportation, retail, education, IT services, and electronics that have fallen victim to the spear-phishing attacks. These sectors, when coupled with the attack's infrastructure and use of Carbanak malware, has FireEye convinced that a threat actor known as FIN7 is behind the malicious emails. It just doesn't know what the group is up to just yet. But FireEye explains FIN7 has plenty to gain from the campaign:
"We have not yet identified FIN7’s ultimate goal in this campaign, as we have either blocked the delivery of the malicious emails or our FaaS team detected and contained the attack early enough in the lifecycle before we observed any data targeting or theft. However, we surmise FIN7 can profit from compromised organizations in several ways. If the attackers are attempting to compromise persons involved in SEC filings due to their information access, they may ultimately be pursuing securities fraud or other investment abuse. Alternatively, if they are tailoring their social engineering to these individuals, but have other goals once they have established a foothold, they may intend to pursue one of many other fraud types."
One of the best ways for companies to defend against this campaign is to conduct security awareness training with their employees. Their efforts should involve a phishing simulation component that urges employees to be on the lookout for suspicious emails, including those that say they're from SEC but contain no logos/personalization and only a few words.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

