
The US Cybersecurity and Infrastructure Security Agency (CISA), FBI, and others have issued a joint alert, advising organisations of the steps they should take to mitigate the threat posed by BianLian ransomware attacks.
BianLian, which has been targeting different industry sectors since June 2022, is a ransomware developer, deployer and data extortion group which has predominantly targeted enterprises.
In recent months the group's attack model has changed from one where financial, business, client, and personal data has been exfiltrated for leverage followed by encryption of victims' systems to one which primarily steals data while leaving systems intact.
Following a typical attack, the BianLian group will threaten that their corporate victim will suffer financial, business, and legal consequences if a ransom payment is not made.
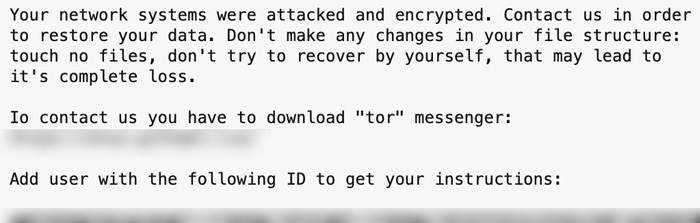
Part of the ransom message left by the attackers reads:
You should know that we have been downloading data from your network for a significant time before the attack: financial, client, business, post, technical and personal files.
In 10 days - it will be posted at our site [REDACTED] with links send to your clients, partners, competitors and news agencies, that will lead to a negative impact on your company: potential financial, business and reputational loses.
In its advisory, CISA advises that BianLian attackers initially gain access to their victims' networks by exploiting compromised Remote Desktop Protocol (RDP) credentials, which have likely either been acquired from other malicious hackers or gathered via phishing attacks.
Once they have gained access, the malicious hackers plant backdoor code, written specifically for each victim and install remote management and access software to maintain access to systems.
In the 19-page joint alert, organisations are urged to lock down RDP, disable commandline and scripting activities and permissions, restrict the use of PowerShell, ensure that only the latest version of PowerShell is installed and that enhanced logging is enabled.
Other advice includes adding time-based locks that prevent the hijacking of admin user accounts outside normal working hours, not storing plaintext credentials in scripts, and implementing a recovery plan that maintains offline, secure backups of data.
There's much more advice on steps organisations can take, as well as indicators of compromise, in the full advisory, which is well worth a read.
In the advisory, once again, the FBI and CISA advise companies hit by ransomware not to give in to the extortion demands as there can be no guarantee that exfiltrated files will not still be published or sold to other criminals:
"Furthermore, payment may also embolden adversaries to target additional organizations, encourage other criminal actors to engage in the distribution of ransomware, and/or fund illicit activities."
Editor's Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

