
Organizations around the world are taking a more innovative approach to managing threats in today’s digital era, reveals the 19th annual Global State of Information Security Survey (GSISS). This year’s study – produced by PwC in conjunction with CIO and CSO – includes the responses of more than 10,000 business and IT security executives from over 130 countries. “Most organizations no longer view cybersecurity as a barrier to change or as an IT cost,” states PwC. Instead, forward-thinking organizations understand that an investment in cybersecurity can foster innovation, enable business growth, and fuel competitive advantage. Below is a quick-read summary of some the main takeaways from the 2017 GSISS:
1. Implementing New Safeguards for Digital Business Models
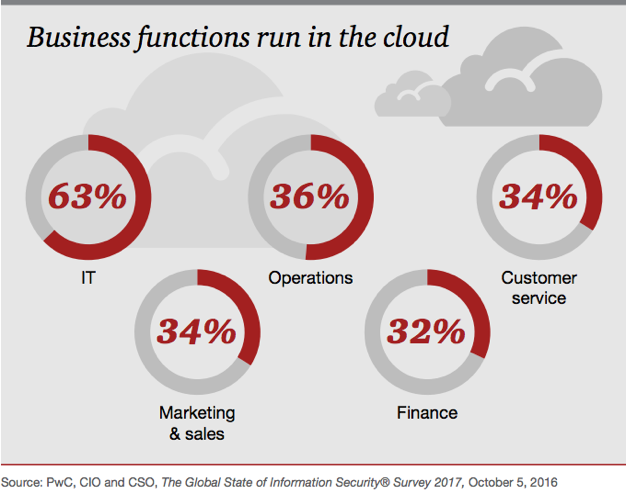
At the core of a more agile cybersecurity approach is the cloud, says PwC. “The power and interoperability of cloud-based platforms enables organizations to synthesize a range of synergistic technologies,” reads the report. In fact, the majority of survey respondents (63 percent) said they run IT services in the cloud, meaning more organizations are entrusting sensitive business functions to cloud providers.
David Burg, PwC’s US and Global Leader of Cybersecurity and Privacy, notes this trend will likely continue as the benefits become increasingly clear:
“The fusion of advanced technologies with cloud architectures can empower organizations to quickly identify and respond to threats, better understand customers and the business ecosystem, and ultimately, reduce costs.”
2. Adopting Threat Intelligence and Information-Sharing
When it comes to anticipating and detecting threats, organizations are also focusing on implementing business-critical threat intelligence and information-sharing programs. According to the report, just over half (51 percent) of this year’s survey respondents said they use Big Data analytics to model for cybersecurity threats and identify incidents.
“What’s needed is advanced analytics and real-time threat intelligence to gain contextual awareness of risks and understand the tactics, techniques and procedures of adversaries” (pg. 13).
The cloud continues to play a vital role in this initiative, providing a single, secure platform for storing and sharing information with others, including business peers, industry groups and government agencies. In turn, this makes monitoring and analysis tools considerably more powerful, the report adds.
3. Embracing Outside Resources
For resource-constrained organizations, managing security from the outside has proven significantly valuable. Nearly two-thirds (52%) of respondents revealed they use managed security service providers (MSSPs) to operate and enhance their cybersecurity programs. A primary driver for this is the global shortage of skilled cybersecurity specialists, which the report goes on to explain is leading organizations to turn to third parties to help run their highly technical initiatives such as authentication, data loss prevention, and identity and access management.
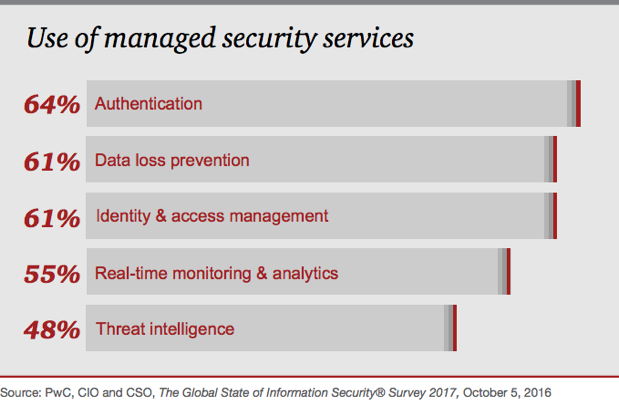
“With the fast pace of technology disruption, keeping up to date with skill sets around new technologies . . . is more and more difficult for organizations,” adds Grant Waterfall, PwC’s global cybersecurity and privacy co-leader.
“Managed security services enables them to procure those skill sets from a service provider and get the niche-specific skills they need to augment their own capabilities.”
4. Securing the Internet of Things
The number of Internet-connected products and services is growing at an unprecedented pace, bringing not only a myriad of opportunities but also security and privacy concerns. To address these risks, PwC says many organizations are proactively updating data-governance policies, assessing devices and technologies, as well as allocating spending to secure IoT devices and systems. According to the report, 46 percent of respondents are investing in an IoT security strategy – up 10 percent from the previous year.
5. Addressing Regulatory Changes
Lastly, complying with a slew of new cybersecurity and data privacy regulations such as the EU GDPR will likely pose serious challenges for global businesses. Among survey respondents, the most-cited privacy issues expected to take priority over the next 12 months are privacy and training awareness (38 percent). They are closely followed by updating of privacy policies and procedures (36 percent).
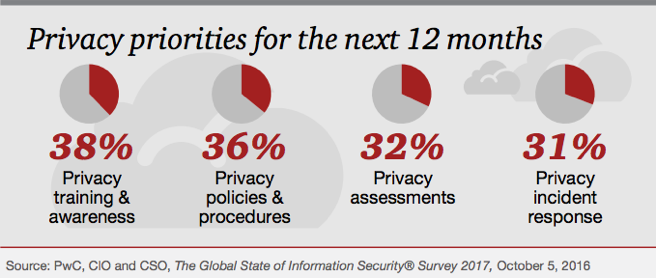
Impacted organizations may be required to conduct comprehensive risk assessments, implement end-to-end security enhancements, and introduce processes and technologies for maintaining data inventories. “Only the proactive will be prepared,” warns the report.
“Organizations can help get ahead of the regulation by conducting a GDPR readiness assessment, remediating GDPR gaps to a alevel of operational adequacy and instituting an ongoing compliance-monitoring process” (pg. 20).
Conclusion This year’s findings reveal most organizations are boosting their security spending as a result of digitization and leveraging their security and privacy programs as a way to enable business growth. But as technology reshapes cybersecurity and privacy models, one mainstay remains constant, adds the PwC report. “Security fundamentals are the sine qua non of an effective program,” it reads.
“Organizations that hew the basics of cybersecurity—fundamentals such as employee training, up-to-date policies and controls, and a commitment to readiness and resilience—will likely be better prepared to manage simple attacks and preserve resources for more complex incidents.”
For more information, read the full Key Findings from The Global State of Information Security Survey 2017 report (PDF).

