
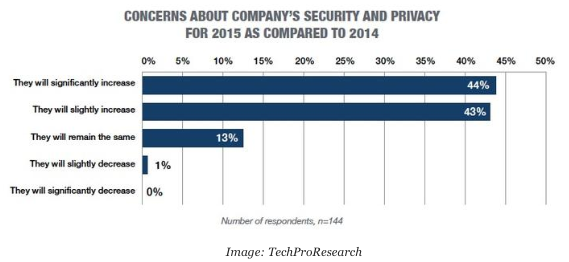
Major cyber security incidents continue to hit the headlines. Security and privacy are top concerns for IT and security professionals, especially after 2014’s highly publicized data breaches. Companies around the globe were victim to malware, stolen data and exploited vulnerabilities. Big companies weren’t immune to this, with Target, JPMogan Chase, Home Depot and Sony Pictures suffering the painful sting of data breaches. Even celebrities were targeted, with compromised iCloud accounts. It really isn’t surprising that almost everyone anticipates the need to prepare for security challenges in the coming months. According to a recent survey by Tech Pro Research, 84 percent of IT professionals are more concerned about security and privacy in 2015.
2014 was a wake-up call for organizations, leaving many wondering how they can bridge this gap between discovering an attack, responding and finally putting measures in place to avoid it from happening again. At Tripwire, we call this the Enterprise Cyberthreat Gap. It is a model that helps understand and address critical gaps across the three lifecycle phases of threat protection.
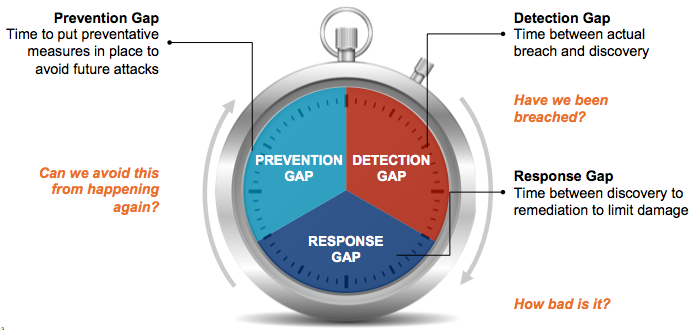
The Detection Gap: With ever increasing zero-day and targeted attacks, it is harder to detect Have we been breached? Where is it? The Response Gap: There’s not enough time or resources to fix everything, so how do you reduce risk most effectively? How do I limit the damage? Is it business critical? The Preventive Gap: Finally, we want to avoid repeated attacks. Can I ensure avoid this from happening again? And reduce my attack surface to continuously reduce risk? The good news is that there's technology innovation at work. At Tripwire, we have seen our customers leverage our deep change detection capability of Tripwire to identify suspicious changes, prioritize them, investigate and then escalate for remediation. Now, they are making investments into next generation threat intelligence solutions. Try integrating both of these together and you’ve got dynamic, advanced threat detection and response. This convergence of security controls depends on two very important capabilities – the ability to integrate and the ability to automate. Integration allows sharing of critical data between controls, while automation acts upon that shared data. At Tripwire we’ve created partnerships, through our Technology Alliance Partner program, with leaders in the threat intelligence market, including Check Point Software Technologies, Palo Alto Networks, Cisco, Lastline, Soltra, CrowdStrike, and iSIGHT Partners, to bring together the best information to make the best and most timely decisions. Together, these combined solutions integrate network and endpoint security together to improve the accuracy and time to detect and protect against advanced threats. Let’s show you how this works with a few use cases.
Advanced Malware Identification to Quickly Identify Potential Threats
The first is advanced malware identification - when we see binaries change and if they behave in suspicious ways.

With Tripwire, you can choose from best of breed threat intelligence solutions available from a number of partners we integrate with. The threat intelligence service analyzes the file and reports back to Tripwire Enterprise letting you know if it is a benign file or if it is a known threat. From there, Tripwire Enterprise provides all of the benefits of its workflow process to drive remediation based on the properties you've set. Also, information about that malicious file and its behavior is now part of the threat intelligence service database and can also be pushed out to Intrusion Prevention Systems and Network Firewalls to block the file at the network level preventing further infection.
Automated Threat Monitoring to Reduce the Attack Surface
Another way we are leveraging this intelligence is through automated threat monitoring – automatically downloading Indicators of Compromise or, as they are commonly called, IOCs.
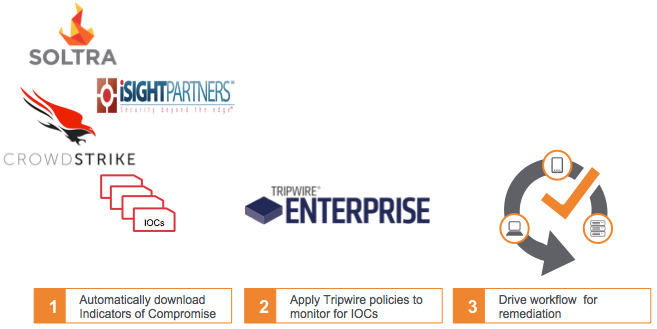
With Tripwire you can take in peer and community sourced indicators of compromise, leveraging STIX and TAXII standards, or through tailored commercial threat intelligence services. Tripwire proactively identifies indicators of advanced threats and targeted attacks or IOCs. These IOCs are automatically downloaded to Tripwire Enterprise where it will search forensics data to see if it is already in the database or something that has never been seen before. Tripwire will then also start monitoring for this IOC in all new changes. If a threat is detected, you get alerted and can drive remediation based on the properties you have set in Tripwire. The end result brings us back to the ultimate goal of closing that Enterprise Cyberthreat Gap by quickly detecting and responding to these advanced threats. Interested in learning more? Here are some of the resources we have available:
- Check out our other technology alliance partners, and download the integration
- Watch our webinar with Wendy Nather, Research Director, 451 Research, on zero-day threats and how to get ahead of the attackers
- Request a demo
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

