
Researchers detected three apps that leverage clever tactics to hide on Android devices so that they can display adware to users. The three adware distributors (com.colors.drawing.coloring, hd4k.wallpapers.backgrounds, and launcher.call.recorder) each had more than 10,000 downloads when Bitdefender Labs first came across them. Its researchers think these apps wouldn't have received so much attention from users had they not come with some legitimate functionality. In fact, a closer look by the research team revealed that the apps were fully functional. This could mean the apps were legitimate when their creators submitted them to the Google Play Store for vetting. That being said, users began flagging the apps as malicious beginning in May 2019. It wasn't long thereafter that Google removed the programs from its Play Store. Bitdefender's researchers took a closer look and found numerous indicators of malicious activity hidden in these three apps. For instance, they found that the programs adopt the Google Play logo as their settings icon and change their settings name to "Google Play Store" shortly after installation. These modifications help the apps conceal themselves from untrained users who might at one point wish to uninstall them.
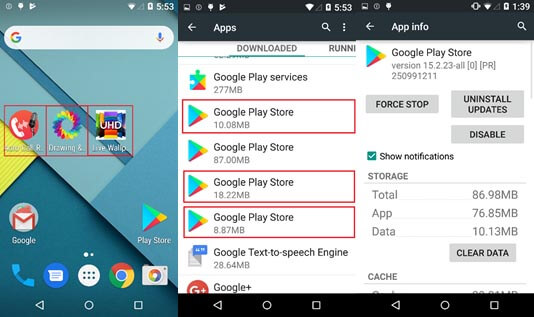
A snapshot of the three apps masquerading as Google Play Store. (Source: Bitdefender Labs) Interestingly, Bitdefender also discovered that the Android apps behave normally without a web connection. For those connected to the Internet, however, the apps hide their icons and close within five seconds, display “Uninstall finished.” or “This app is incompatible with your device!” as an error message and open the real Google Play Store to an app that's already installed on the device. Each app employs these tactics as a means to confuse the user while surreptitiously launching its malicious functionality so that it could begin distributing adware. As Bitdefender Labs explains in its research:
The app will also set an alarm with a 24-hour delay. When this alarm is triggered, a new class OneWork is executed. This class sets one alarm with a 15-minute delay and another with a 24-hour delay. The 15-minute alarm will start the class AdWorker, which starts an overlay add. From this point on, it will reschedule itself every 15 minutes, ensuring that the ads are constantly displayed on the victim’s device.
These apps all made it to Google Play Store by way of different developers. But it's not impossible that one coder created all of them for the purpose of spreading adware. News of these apps arrives more than two years after researchers found dozens of Android applications available on Google Play delivering a strain of adware capable of collecting users’ personal information.

