
Understandably, a few eyebrows raise up when I suggest today’s cybersecurity challenges started nearly 370 years ago, some 300 years before the invention of ENIAC (the world’s first digital computer). But I stand by this observation because of the unintended clash of two systems: the nation-state and the Internet. Many of the institutions, social constructs and domains we have accepted as norms came out of the Peace of Westphalia, a series of treaties to end the 30 Years War. No, the problems do not stem from the fact that many of us wish to throw our devices out the window when things go wrong or we find ourselves in disagreement with technology. (Though defenestration does sometimes feel like a natural response to many of our cybersecurity problems.) Rather, the problems stem from the boundaries that the Peace of Westphalia established. Consider the three principles that the Peace of Westphalia established:
- Sovereignty
- Legal equality
- Policy of non-interventionism
In lay terms, these principles translate into the following: defined boundaries, jurisdiction, and “keep out of my house.” These basic principles have served – and continue to serve – as the bedrock principles of our foreign relations, forming the system we know today: the modern-day nation-state. Without this system of the nation-state, it is quite possible continental Europe would have spun further out of control, continuing to tear itself apart, as it was in the 15th and 16th Centuries. If that chaos had continued, the world would certainly look much different today. In the simplest sense, the Peace of Westphalia established norms that most persons (particularly of the ruling class) were willing to accept. Even those who have wildly different worldviews on how to live life are able to agree on what “a country” is. (Disclaimer: okay, I am not as confident as I was a couple of years ago on this argument given recent social discourse and public debate.) Fast forward to the 1960s, and we see how the clash of systems begins. The development of ARPANET (the beginning of the Internet) and the years shortly thereafter spurred a debate regarding what type of controls the network should have. Fred Kaplan’s book Dark Territory: The Secret History of Cyber War sheds light into this debate with some detail, but I will try to simplify: should the network be secured in some manner with controls, or should the network be open, allowing the freest flow of information sharing? The latter argument eventually won out (which is why the Internet today is inherently vulnerable), but I hope you are starting to see how this emerging system (the Internet) has developing features that are in direct opposition to an established system (the nation-state). We can define three developmental features of the Internet:
- There is no established sovereignty.
- Legal blurring is prevalent.
- By virtue, the Internet is interventionist and disruptive in nature.
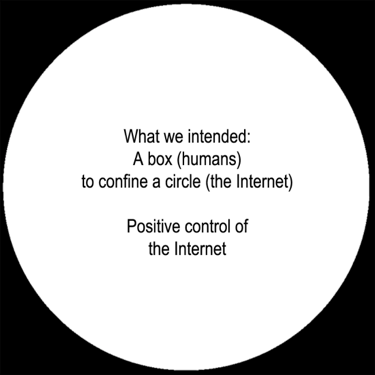
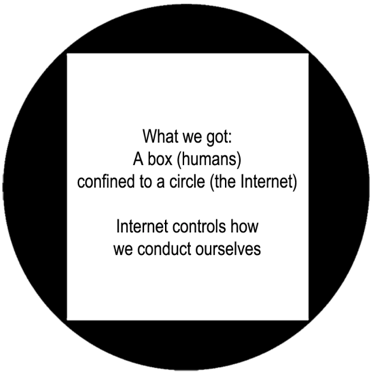
Or to put it another way, the Internet is: free of boundaries, has no jurisdiction (from a practical enforcement perspective at least), and is “in everybody’s house.” Therefore, it should come as no surprise to any one of us that we are having such a hard time trying to solve the most difficult challenges in cyberspace when these two systems are in constant conflict. (With all respect to my technologist friends, patching a critical vulnerability or tracking down malicious code that is making your system go bonkers is an easy challenge compared to this one.) And with that said, here is the real noodle bender: we (humans) created the Internet with the intent of confinement as a means of positive control. (Note: “control” is not nefarious (or conspiratorial) in this case. Rather, “control” is analogous to having a “hand on the wheel” to make sure you do not drive off a cliff.) Instead of positive control, we have a system that completely controls how we conduct ourselves. Hopefully, the diagrams below help visualize what I am presenting:
I challenge anybody not living under a rock to prove otherwise. The Internet touches every aspect of our lives. Your reading this is proof of this, as there is no way I could reach you in the manner that I have by traditional print means. It is simply too expensive, and the distribution channels are not accessible to me without heavy investment in capital (which most people do not have, by the way). This change in control matters because it alters everything we do from foreign relations, business, cultural interaction and even personal relationships. Furthermore, this change in control allows actors to attempt unfettered interference into another actor’s business that was simply impossible in the past. Whether interference is successful is up for debate, though commentary and opinion on the matter has run amok. And I will qualify that statement: interference is successful, but the degree to which that interference had a meaningful impact is up for debate and incredibly difficult to measure. Measurement, at best, is limited to a subjective analysis. As indicated in my previous article, many of today’s cyber challenges are an extension of some pre-existing conflict happening in the physical domain, but it is the tools that are incredibly different and much more powerful in some corners. Would the Arab Spring of 2011 played out as it had if social media networks had not been present? Would the 2016 US Presidential Elections played out differently? Of course they would have, but to act as some clairvoyant and confidently state “if x didn’t occur, then y would have happened” is a hard argument for me to accept when there are millions – billions – of factors at play. What I will accept is that there is level of asymmetry and disproportionate impact that we are not accustomed to seeing all because of these systems in opposition. This is all the more reason why identifying these issues (and properly labeling them) matter. In the next article, I will elaborate further on this clash and how national interests will continue to take precedent over any other interest for the foreseeable future. FBI Director James Comey in his May 3, 2017 testimony in front of the Senate Judiciary Committee presented some very nuanced and important comments, which illustrate how profound this clash of systems is. More importantly, the comments reinforce how much of the cybersecurity challenge requires further and deeper human understanding of the issues.

About the Author: George Platsis has worked in the United States, Canada, Asia, and Europe, as a consultant and an educator and is a current member of the SDI Cyber Team (www.sdicyber.com). For over 15 years, he has worked with the private, public, and non-profit sectors to address their strategic, operational, and training needs, in the fields of: business development, risk/crisis management, and cultural relations. His current professional efforts focus on human factor vulnerabilities related to cybersecurity, information security, and data security by separating the network and information risk areas. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

