
Once again, researchers have uncovered security flaws that could allow malicious hackers to attack implanted medical devices, such as heart pacemakers and cardiac defibrillators, with the potential to deliver fatal shocks. In a newly-published paper, "On the (in)security of the Latest Generation Implantable Cardiac Defibrillators and How to Secure Them" (PDF), researchers from KU Leuven University, Belgium, the University of Birmingham, and University Hospital Gasthuisberg describe their disturbing findings. The researchers reverse-engineered the communication protocols employed by at least 10 widely-used defibrillator implants (ICDs) to communicate over long-range RF channels (2-5 meters). Using inexpensive off-the-shelf equipment, the researchers were able to find weaknesses in several protocols and their implementation, and they demonstrated that they could steal telemetry information, launch battery-draining denial-of-service attacks, and even transmit unauthorised commands that could compromise the safety of patients.
"Adversaries may eavesdrop the wireless channel to learn sensitive patient information, or even worse, send malicious messages to the implantable medical devices. The consequences of these attacks can be fatal for patients as these messages can contain commands to deliver a shock or to disable a therapy."
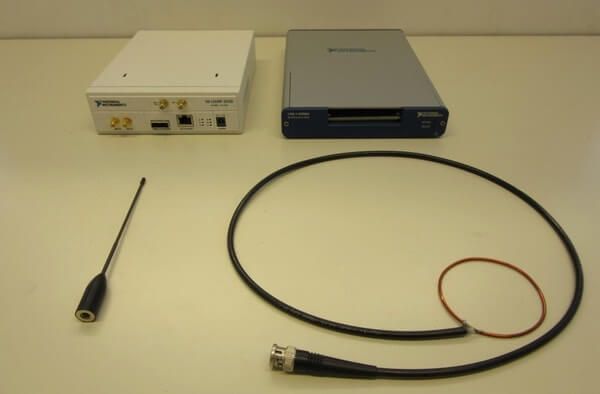
What makes the research all the more disturbing is that no prior knowledge of the medical devices being used was required. Instead a "black box" set up in the research lab scrutinised the legitimate wireless communications as they were sent, hunted for weaknesses, and helped fully reverse-engineer proprietary protocols.
"Our results demonstrated that security-by-obscurity is a dangerous design approach that often conceals negligent designs. Therefore, it is important for the medical industry to migrate from weak proprietary solutions to well-scrutinised security solutions and use them according to the guidelines. Our work revealed serious protocol and implementation weaknesses on widely used ICDs, which lead to several active and passive software radio-based attacks that we were able to perform in our laboratory."
As The Register reports, the vendor of the compromised devices is said to have issued a patch. But one wonders how many implanted medical devices may still be at risk. Threats against medical implants are not just the realm of thrillers; they are genuine concerns. If any further proof is needed, just consider that former US vice-president Dick Cheney had the wireless feature of his implanted heart defibrillator deactivated due to the potential for it to be exploited by assassins. https://www.youtube.com/watch?v=JQY2QQ94Q-o&rel=0 For more information about the security of medical devices, be sure to check out the website of I am the Cavalry, a group of security researchers who finds it concerning that the health care sector is trailing many years behind banking and retailers when it comes to protecting against online threats. I am the Cavalry published its own "Hippocratic Oath for Connected Medical Devices" earlier this year, hoping to encourage manufacturers to take security more seriously. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc. Save
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

