
An attack campaign leveraged the Excel VelvetSweatshop encryption technique to deliver samples of the LimeRAT malware family. According to Mimecast, those responsible for this attack campaign turned to VelvetSweatshop to enhance the efficacy of their efforts. Nefarious individuals have a history of using a password to encrypt malicious Excel spreadsheets. Doing so helps their attack emails bypass anti-malware detection tools. All they need to do is to include the password in their phishing emails, as recipients need to submit the password when they attempt to open the spreadsheet.
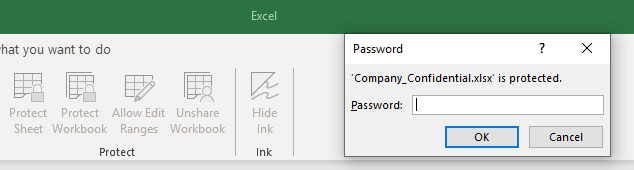
A password is needed to get access to a locked Excel file (Source: Mimecast) Malicious actors' decision to use "VelvetSweatshop" as the password helped streamline this attack chain. That's because Excel in general attempts to use VelvetSweatshop as an embedded default password for the purposes of decrypting a file, opening it in read-only mode and running on-board macros. Only if VelvetSweatshop fails does Excel prompt the user to enter a password. In using VelvetSweatshop as their encryption technique, those behind this campaign therefore removed the need for users to receive and submit a password. All the victim needed to do was double-click on the file. As explained by Mimecast:
The advantage of the read-only mode for Excel to the attacker is that it requires no user input, and the Microsoft Office system will not generate any warning dialogs other than noting the file is read-only. Using this read-only technique, the attacker can reap the obfuscation benefits of file encryption without requiring anything further from the user, taking away one step required of the intended victim for exploitation to occur.
Once opened, the Excel document delivered a sample of LimeRAT malware. This infection gave attackers the ability to initiate a cryptomining session, encrypt the recipient's data, log the victim's keystrokes and/or perform other malicious functionality. The attack described above highlights the need for organizations to defend against sophisticated email-borne threats. They can do this by educating their employees about some of the most common types of phishing attacks that are in circulation today. Additionally, they should consider investing in a tool like Tripwire File Analyzer that can analyze suspicious files and provide reports on relevant system changes.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

