
Attackers are using a copycat version of WannaCry ransomware dubbed "WannaLocker" to target Android users living in China. WannaLocker has been targeting Chinese gaming forms disguised as a plugin for King of Glory, a popular Chinese game. Upon installation of this fake add-on, the threat conceals its icon from the Android app drawer and changes the main wallpaper to an anime image. It then begins encrypting files stored on the device's external storage.
Fake King of Glory plugin. (Source: AVAST) It's been a while since the security community has seen a threat that targets an Android device's external storage for encryption. In 2014, researchers at Slovakian IT security team ESET detected Android/Simplocker. This trojan scans the device's SD card for peg, jpg, png, bmp, gif, pdf, doc, docx, txt, avi, mkv, 3gp, mp4 file types and encrypts every instance it finds before issuing a ransom demand. Back then, Simplocker requested 260 Ukrainian Hryvni, which is approximately 10 USD today. This latest Android threat employs AES encryption to taint a user's files. But it does have a few exceptions. For instance, it doesn't encrypt files that include "DCIM", "download", "miad", ”android", or "com." in the path; files that are bigger than 10 KB; or files that begin with "." character. One it completes its encryption routine, it demands even less than Simplocker, and it uses a ransom message clearly inspired by WannaCry's note to reveal its orders.
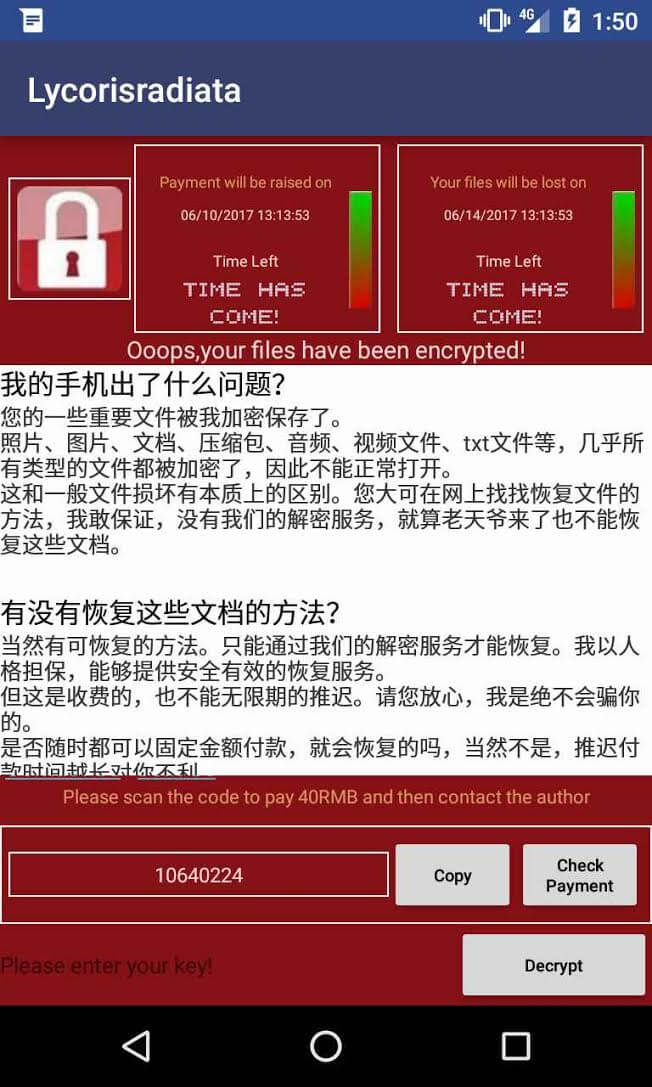
WannaLocker's ransom screen. (Source: AVAST) Nikolaos Chrysaidos, head of mobile threat intelligence and security at Avast, explains more in a blog post:
"The ransomware then demands a ransom of 40 Chinese Renminbi, which is equivalent to about 5-6 US dollars. This is not much compared to what other mobile ransomware has demanded in the past. The fact that the ransom is being demanded in regular currency and not in cryptocurrencies makes me think the people behind this are trying to make money, and fast. This is, however, risky as the money can be easily traced, unlike when sending cryptocurrencies."
The ransomware informs victims to pay using QQ, Alipay, or WeChat. Android users can protect their phones against threats like WannaLocker by installing a mobile anti-virus solution on their phones. They should also refrain from downloading apps on any app marketplaces besides Google Play. But even these steps don't automatically protect them against a ransomware infection. Just in case they become victims of a ransom-based attack, they should back up their mobile data regularly.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

