
A newly detected worm is propagating through removable drives to distribute a fileless variant of the BLADABINDI backdoor. In mid-November, researchers at Trend Micro first observed the worm, which the security firm detects as "Worm.Win32.BLADABINDI.AA." They're still investigating the threat's exact method for infecting a system. But after analyzing its propagation routine, the researchers determined that the worm likely propagates and enters a system through removable drives. Specifically, they spotted the worm installing a hidden copy of itself on any removable drive connected to the infected system. Trend Micro found that the worm was using AutoIt to compile the payload and main script into a single executable, thereby complicating detection. With the help of an AutoIt script decompiler, the researchers identified the worm's use of an auto-run registry that employs PowerShell to load the encoded executable as a fileless threat from memory and not from the system's disks.
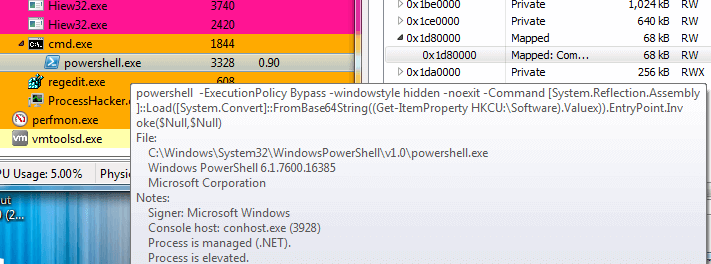
Screenshots showing PowerShell loading the encoded executable. (Source: Trend Micro) The loaded executable, a variant of the BLADABINDI backdoor, uses port 1177 to connect to its command-and-control (C&C) server at water-boom[.]duckdns[.]org. This URL uses dynamic domain name system (DNS), which allows attackers to change or update the server's IP address. After creating a firewall policy allowing PowerShell, BLADABINDI then enables attackers to activate a keylogger, execute files and steal credentials from web browsers. Trend Micro doesn't downplay the threat posed by BLADABINDI, malware which previously preyed on wannabe attackers’ interest in cracking a target’s Facebook account. As the security firm's researchers explained in a blog post:
The worm’s payload, propagation, and technique of filelessly delivering the backdoor in the affected system make it a significant threat. Users and especially businesses that still use removable media in the workplace should practice security hygiene.
Organizations can ensure this level of security hygiene with the help of the Center for Internet Security's Critical Security Controls. Specifically, they can use Control 8 to to configure anti-malware scanning of removable media. They can also use Control 13 to manage the system's external removable media's read/write configurations.

