
A security researcher discovered a new ransomware strain called "Zorab" masquerading as a decryptor for STOP Djvu ransomware. Michael Gillespie, creator of the Ransomware ID service, spotted Zorab being distributed as a decryptor for the STOP Djvu family. A relatively common ransomware strain, STOP Djvu was involved in various digital attacks over the past year or so. Back in January 2019, STOP used adware installers disguised as cracks as a new method of distributing itself to unsuspecting users. That was just a couple of months before researchers spotted a variant of the STOP ransomware family downloading the Azorult infostealer onto victim’s machines as part of its infection process. The attack began when victims entered their information into a fake STOP Djvu decryptor and clicked a "Start Scan" button. In the process, the program extracted another process called "crab.exe" and saved it to %Temp% folder. Bleeping Computer explained what happened next in the infection chain:
Crab.exe is another ransomware called Zorab, which will begin to encrypt the data on the computer. When encrypting files, the ransomware will append the .ZRB extension to the file's name. The ransomware will also create ransom notes named '--DECRYPT--ZORAB.txt.ZRB' in each folder that a file is encrypted. This note contains instructions on how to contact the ransomware operators for payment instructions.
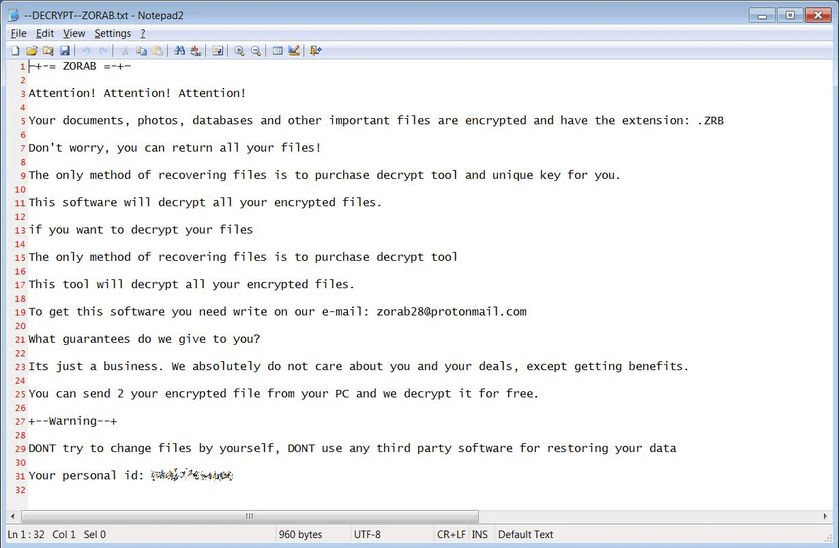
Zorab's ransom message (Source: Bleeping Computer) At the time of writing, Gillespie was in the process of analyzing the ransomware to determine whether he could exploit a flaw for the purpose of creating a free decryption tool. This threat highlights the danger of meeting ransomware attackers' demands. There's no guarantee that you'll be able to recover your data if you pay a ransom. As Zorab demonstrates, you might end up suffering another ransomware infection in the process, as well. Acknowledging those risks, organizations and users alike should focus on preventing a ransomware infection in the first place. They can use these steps to do so.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

