Respond to What‘s Happening in Your Environment
The Tripwire®️ LogCenter®️ correlation engine automatically identifies and responds to events of interest. Actions can include creating a work ticket, sending a notification email, or running a command. It also integrates with Tripwire Enterprise and Tripwire IP360 to detect and respond to anomalies and suspicious activities.


Automate Compliance Evidence
Ensure you meet regulatory requirements for log collection and retention. Store and forward log data using a lightweight agent that overcomes system failures to ensure your data isn't lost. Get started quickly with security solution packs for insider threats, user audit, authentication, DoS detection, breach detection, and intrusion detection.
Filter Relevant and Actionable Data
Reduce the workload and costs associated with traditional SIEMs and security analytics solutions. Pre-filter data and identify anomalies and patterns known to be threats and early indicators of breaches.
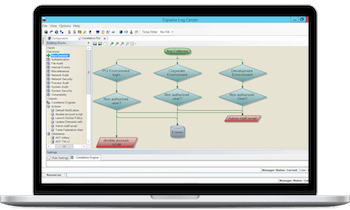
Get to Know Tripwire LogCenter
Not Sure Which Product Is Right for You?
Contact one of our security and compliance experts to understand your needs and match them with the best Tripwire solution.