Tripwire provides an integrated suite of solutions to help solve security challenges facing organizations within today’s Department of Defense. Tripwire tools have been used within government and military organizations in both tactical and non tactical environments to ensure system hardening through security configuration management, real time threat detection with continuous monitoring, and data storage and analytics for faster incident response. Tripwire helps reduce cybersecurity risks while maintaining government compliance standards through continuous discovery, profiling, assessment, monitoring and mitigation of their IT infrastructure.
Tripwire enables organizations to reduce IT security risks while maintaining compliance with industry and/or government regulations through continuous discovery, profiling, assessment, monitoring and mitigation of their IT infrastructure. Tripwire products align with Best Practice Frameworks enabling the customer to follow widely accepted process or control frameworks such as SANS 20 CSC, TIL, NIST RMF (800-37), NIST 800-53, DISA Polices/ STIGs, PCI and SCAP and more. Tripwire has obtained Army CoNs and ATOs in the Air Force and NSA. In addition, Tripwire monitors and protects systems in major Army commands, and is installed in every major cabinet level civilian agency. Tripwire has also developed custom policies that monitor and detect vulnerabilities in the active cyber defense (ACD) initiative. Cyber Protection Organizations require timely and actionable information. It requires operational context that is prioritized for quick response, or that information will have limited actionable value.
Tripwire delivers unprecedented risk visibility, mission/operational context and security business intelligence. We enable enterprises to protect sensitive data and assets from breaches, vulnerabilities and threats through our trusted portfolio of high priority security control solutions that include:
- Security Configuration Management (SCM)
- Vulnerability Intelligence
- File Integrity Monitoring (FIM)
- Automated Continuous Diagnostics and Mitigation (CDM)
- Log Intelligence
- Granular Vulnerability Scoring and Prioritization
- Real Time Change Detection
- Advanced Analytics and Reporting
The Tripwire security suite can monitor over 125 operating systems and applications for change including Window, Mac OS, Linux, virtual infrastructures, databases and network devices. This enables Tripwire to detect leading indicators of breach activity across the enterprise, dynamically protect mission critical systems, and make security efforts visible, measurable and action able. Tripwire has a portfolio of solutions that are unique in delivering cyberthreat security that provide:
- Detection indicators of breach, compromise and vulnerability
- Relevant operational context connecting security efforts to mission and operational goals and minimizing risks
- Automation with applied intelligence to deliver more effective operations
- Enterprise integration across the Tripwire portfolio, as well as with your existing and future security ecosystem
With Tripwire’s combined set of security controls you can monitor your environment for events of interest in real time, track configuration changes and identify vulnerabilities before they are exploited.
Tripwire provides practical Security Information and Event Management (SIEM) in a tactical or non tactical environment through Operational and System Architectures implemented throughout an organization’s Cyberspace/Battlespace.
The Tripwire suite provides operators with deep security intelligence, providing visibility into otherwise overwhelming and disjointed data from siloed security controls. Tripwire adds rich context to security events and decreases the time and effort required to identify and respond to security incidents. Tripwire’s Security Configuration Management provides leading indicators of breach activity by being aware of the state of systems, how they’re configured and whether they’re configured according to current policy. Once a known and trusted state is achieved, Tripwire continuously monitors for changes and deviations from your baseline. Tripwire’s Event Integration Framework overlays log intelligence and event data to detect suspicious events and enables security context and prioritization.
INSIDER THREATS
Managing the risks an insider threat poses to an organization requires a combination of people, process and technology. Although it may seem like an impossible task to mitigate damage caused by insider, there are usually indicators that can identify potential risk before an incident occurs. By aligning communication and policies between Human Resources and your IT department you can implement controls to reduce risk and detect incidents before they cause damage.
A FIPS 140-1 AND 140-2 VENDOR
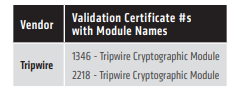
NIST provides a list of all vendors with a validated FIPS 140-1 and FIPS 140-2 cryptographic module. Beside each vendor name is the validation certificate number(s) for the vendor’s module(s) including the module name. Here is the section pertaining to Tripwire’s FIPS 140-2 Certification: