The Health Insurance Portability and Accountability Act (HIPAA) was enacted to safeguard Protected Health Information (PHI) by mandating procedures and controls to assure the public that critical and private information is controlled from loss of confidentiality, integrity or availability. With few exceptions, an organization is subject to HIPAA if it exchanges data related to the health care profession.
The Challenge
Cyberattacks, including ransomware, have become ubiquitous in the healthcare industry. Patient records contain nearly everything an attacker needs in a single record to carry out sophisticated insurance fraud schemes, purchase medical supplies or drugs, or commit other types of fraud including outright identity theft. Recent studies have determined that cyber criminals can sell the comprehensive identity information found in a health insurance or patient record on the black market for as much as $1,000. Compare that to the average cost of a stolen credit card that fetches about $1 on the black market, and it is readily apparent why healthcare organizations are so frequently targeted.
Adding to the complexity of these security challenges are compliance and regulatory frameworks (such as HIPAA, NIST, ISO, PCI and COBIT) typically enacted to protect systems and sensitive data. However, since they frequently evolve to keep pace with information technology, industry influences and new threats to systems and data, healthcare organizations face multiple moving targets for managing controls and meeting requirements. Healthcare organizations, struggling to address ever growing cybersecurity risks with limited resources—the lack of cybersecurity talent and high turnover on cybersecurity teams—typically focus their energies by employing a “checkbox” mentality for passing each HIPAA compliance audit, and then simply return to business as usual after the administrative scramble. This is when configurations can start to drift out of compliance, even though at a particular point in time the organization may have passed an audit.
The Goal: Continuous HIPAA Compliance
Meeting the requirements of HIPAA requires most businesses to set up strong processes, methods and controls to assure auditors that security and integrity of PHI is assured. The specific technical rules are fairly prescriptive, and systems that are in scope for HIPAA should meet both the Act’s intention and the implementation instructions as put forth in Sections 160, 162 and 164. Even if your organization is compliant today, that’s no guarantee of security. Most organizations have IT systems that must be updated, modified and maintained, which introduces the previously mentioned configuration drift. Tripwire has found that most organizations need both a compliance monitoring system and a change control process to assure only authorized change is introduced to in scope systems. System integrity is ensured only by being able to demonstrate to your HIPAA auditor that you have a process that assures only authorized change occurs. Tripwire® ExpertOpsSM can help organizations achieve continuous HIPAA compliance while insulating their teams from the challenges of turnover and the cybersecurity talent gap.
Your Solution: Tripwire ExpertOps
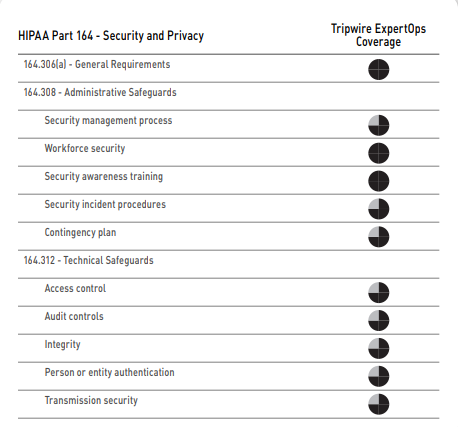
Tripwire ExpertOps combines managed services with the industry’s best File Integrity Monitoring (FIM) and Security Configuration Management (SCM) to help Covered Entities address the requirements of the HIPAA security rule, as outlined in Section 164. Tripwire ExpertOps also provides personalized consulting, HIPAA audit support, and a cloud based infrastructure to help you achieve and maintain compliance. The solution is easy to deploy and use, with simple subscription pricing and a low total cost of ownership.
Tripwire ExpertOps enables you to rapidly achieve compliance with HIPAA by reducing the attack surface, increasing system integrity and delivering continuous compliance. Plus, because Tripwire ExpertOps includes personalized consulting, you receive ongoing support from a designated Tripwire Expert.
Benefits
- HIPAA audit support
- 24/7 compliance visibility via a customized dashboard
- Alerts and reports in your inbox
- Waivers and change requests made easy
- No more awkward or incomplete hand offs when your staff changes
How It Works
Tripwire ExpertOps provides you with continuous staffing to operate and manage Tripwire provided HIPAA controls at peak efficiency. The solution adapts to your unique environment—reports and profiling tasks are customized to meet your specific needs. You will receive expert guidance to configure your system and policy configurations to best align with your requirements. And you’ll gain visibility via 24/7 access to compliance information via a tailored dashboard and management console.
A Tripwire Expert will act as an extension of your team by prioritizing work efforts and managing critical escalations. Together you will jointly develop a Service Plan that outlines communication practices, escalation procedures and any specialized requests.
The Tripwire Expert will then tune and operate your Tripwire provided HIPAA controls to provide:
- Prescriptive policy and content guidance to enable HIPAA compliance for your specific network or system security requirements
- Recommendations for maximizing automation capabilities for compliance and event alerting practices, change management process integrations, and audit prep activities
- Prioritized remediation to identify opportunities to efficiently improve compliance posture
- Quarterly executive review of achievements towards objectives, insight into ongoing improvement, and utility of the environment
- Organizational grading for each accountable department to provide visibility into groups needing additional resources and attention
Get 24/7 visibility without deploying additional hardware, databases and backend software. Tripwire ExpertOps is built on a cloud computing platform, allowing the service to quickly scale to meet your needs while maintaining high levels of security. The service uses a single tenancy model to ensure that data remains segregated between customer accounts. Tripwire applies multiple controls for security and privacy of your data, including secure configurations, vulnerability scanning, data encryption, malware defenses, access control, log management, multi-factor authentication, VPN and much more.
Ready to Take the Next Step?
Get in touch with your Tripwire Account Manager to develop a custom Service Plan for Tripwire ExpertOps.