
A threat actor known as APT33 is actively targeting organizations in the aerospace and energy sectors with spear phishing campaigns. Between mid-2016 and early 2017, the suspected Iranian digital espionage group attacked a U.S. organization in the aerospace sector, a Saudi Arabian conglomerate with aviation holdings, and a South Korean company known for its business in oil refining and petrochemicals. FireEye's threat researchers Jaqueline O’Leary, Josiah Kimble, Kelli Vanderlee, and Nalani Fraser believe APT33 targeted these organizations in an effort to advance Iran's regional interests. As they explain in a blog post:
"We assess the targeting of multiple companies with aviation-related partnerships to Saudi Arabia indicates that APT33 may possibly be looking to gain insights on Saudi Arabia’s military aviation capabilities to enhance Iran’s domestic aviation capabilities or to support Iran’s military and strategic decision making vis a vis Saudi Arabia. "We believe the targeting of the Saudi organization may have been an attempt to gain insight into regional rivals, while the targeting of South Korean companies may be due to South Korea’s recent partnerships with Iran’s petrochemical industry as well as South Korea’s relationships with Saudi petrochemical companies. Iran has expressed interest in growing their petrochemical industry and often posited this expansion in competition to Saudi petrochemical companies. APT33 may have targeted these organizations as a result of Iran’s desire to expand its own petrochemical production and improve its competitiveness within the region."
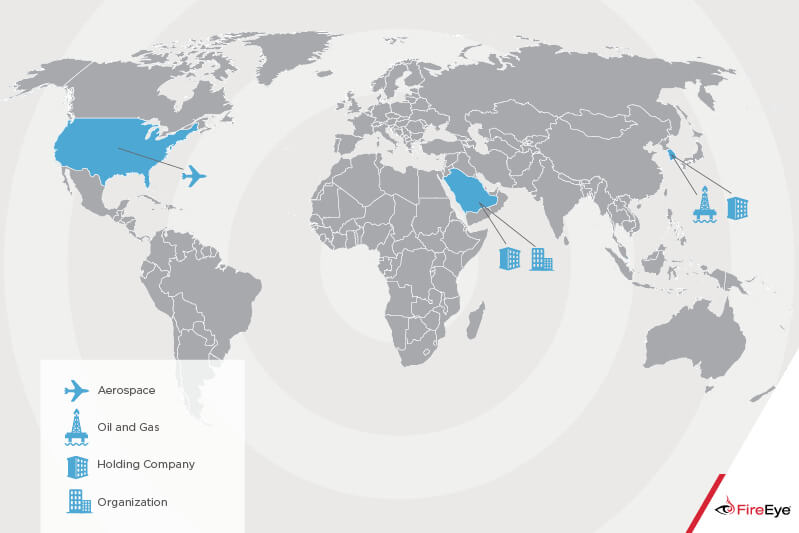
Figure 1: Scope of APT33 Targeting. (Source: FireEye) To infiltrate its targets, APT33 sent out spear-phishing emails to organizations in the aviation sector using fake website domains designed to masquerade as Boeing, Northrop Grumman, and other well-known aviation and military support organizations based in Saudi Arabia and the Western world. The emails lured in the recipient with fake job postings and tricked them into clicking on a link to a malicious HTML application (.hta) file, a type of file which other attackers have leveraged to distribute ransomware. The HTA file, in turn, executed code that downloaded a customized APT33 backdoor. There are several pieces of evidence that link APT33 to the Iranian government. First, an actor operating under the handle "xman_1365_x" was at one point a community manager in the Barnamenevis Iranian programming and software engineering forum before they developed APT33's TURNEUP backdoor. They're also linked to the Nasr Institute, which is believed to be the Iranian government's "cyber army." Additionally, the threat group conducted its attacks in alliance with Iran's regional interests, operated according to Iran's workweek (Saturday-Wednesday), and used hacker tools that are popular in Iran. That's not all. FireEye's threat research team also found evidence linking APT33 to other attack campaigns:
"One of the droppers used by APT33, which we refer to as DROPSHOT, has been linked to the wiper malware SHAPESHIFT. Open source research indicates SHAPESHIFT may have been used to target organizations in Saudi Arabia."
In March 2017, Kasperksy compared DROPSHOT (which they call Stonedrill) with the Shamoon 2.0 attacks. They stated in their report (PDF) that both wipers employ anti-emulation techniques and targeted organizations in Saudi Arabia. To protect against threat groups like APT33, aerospace and energy companies should familiarize their employees with some of the most common types of phishing attacks. They should also consider investing a solution that automates their detection of digital threats via continuous monitoring and change tracking. For information on how Tripwire can protect your organization operating in the energy sector, click here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

