
Cisco has patched a remote code execution (RCE) vulnerability bearing a "perfect" CVSS score of 10.0 that affects its Adaptive Security Appliance (ASA) software. On 29 January, the American multinational technology conglomerate publicly recognized the security issue (CVE-2018-0101) and revealed that it affects the ASA software found in the following 10 Cisco products:
- 3000 Series Industrial Security Appliance (ISA)
- ASA 5500 Series Adaptive Security Appliances
- ASA 5500-X Series Next-Generation Firewalls
- ASA Services Module for Cisco Catalyst 6500 Series Switches and Cisco 7600 Series Routers
- ASA 1000V Cloud Firewall
- Adaptive Security Virtual Appliance (ASAv)
- Firepower 2100 Series Security Appliance
- Firepower 4110 Security Appliance
- Firepower 9300 ASA Security Module
- Firepower Threat Defense Software (FTD)
ASA software delivers firewall capabilities for ASA devices at the enterprise level. It also offers integrated VPN capabilities and facilitates site-to-site VPN on a per-context basis. Essential to the Cisco ASA Family, ASA software makes up part of the Firepower Threat Defense platform, unified software which offers next-generation firewall solutions. The technology company explains how this particular flaw works in a security advisory:
The vulnerability is due to an attempt to double free a region of memory when the webvpn feature is enabled on the Cisco ASA device. An attacker could exploit this vulnerability by sending multiple, crafted XML packets to a webvpn-configured interface on the affected system. An exploit could allow the attacker to execute arbitrary code and obtain full control of the system, or cause a reload of the affected device.
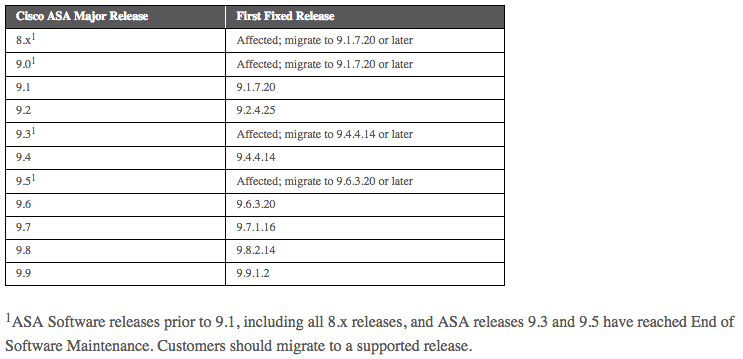
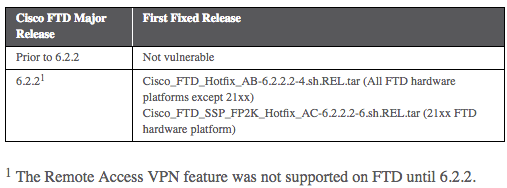
There are no workarounds for this flaw, which has received a CVSS score of Base 10.0. While the Cisco Product Security Incident Response Team (PSIRT) is aware of "public knowledge of the vulnerability," it is not currently aware of any malicious exploits. Customers with ASA devices running ASA software releases prior to 9.1 as well as 9.3 and 9.5 should move to a supported release. There are also updates available for Firepower Threat Defense 6.2.2, the version which first introduced the remote access VPN feature.
The full details about this vulnerability will be released on 2 February. Organizations need to make sure their systems are protected against this vulnerability and others. They can do so by investing in a vulnerability management solution that helps them profile all their network assets and prioritizes bugs based on their business needs. To learn how Tripwire can help in this regard, click here.
Mastering Security Configuration Management
Master Security Configuration Management with Tripwire's guide on best practices. This resource explores SCM's role in modern cybersecurity, reducing the attack surface, and achieving compliance with regulations. Gain practical insights for using SCM effectively in various environments.

