
Tripwire recently hosted a webcast entitled, “PCI Breach Scenarios and the Cyber Threat Landscape with Brian Honan: Real World Cyber Attacks and Protecting Credit Card Data.” For our presentation, Brian Honan (CISM, CGEIT, CRISC), an information systems and cybersecurity specialist and a member of the Advisory Group on Internet Security to Europol’s Cyber Crime Centre (EC3) on breach investigations, joined me to discuss the importance of the new Payment Card Industry Data Security Standard 3.0. Together, we also provided some insight into how companies can leverage this new compliance standard to protect themselves against a security breach. As reported by the 2013 Europol Serious & Organized Threat Assessment, the “Total Global Impact of CyberCrime [has risen to] US $3 Trillion, making it more profitable than the global trade in marijuana, cocaine and heroin combined.” This growing cost of cyber crime partially reflects the different laws that define countries’ breach disclosure policies. For example, whereas the United States has mandatory disclosure laws, the European Union has none. European-based companies that have been affected by an incident, including TK Maxx, Loyaltybuild, Stay Sure and CEC Bank, are therefore under no obligation to notify their customers of an incident. This lack of visibility may limit the affected company’s incentives to invest in detection measures that facilitate a timely response.
“37% of respondents said they were not confident in their ability to detect a breach at all.”-Tripwire Online Survey, March 2015
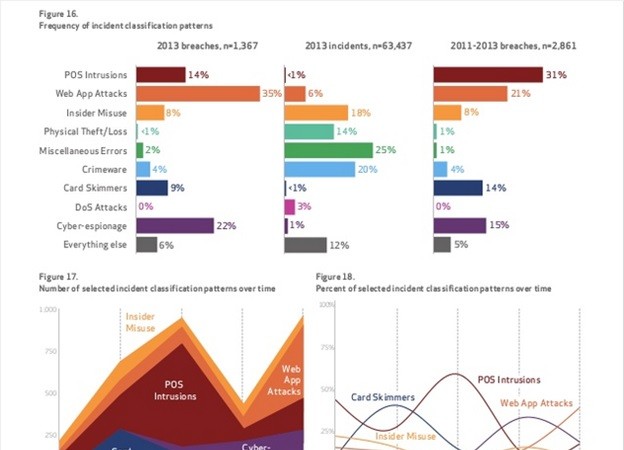
Acknowledging these differences in breach detection and response, we took the opportunity to poll our webcast participants in an effort to gain an understanding of companies’ breach preparedness more generally. First, we asked our participants how long they estimated it would take for them to detect a breach. The responses varied, but most disturbing was the fact that 37% of respondents said they were not confident in their ability to detect a breach at all. This finding is not new, however. In its 2014 Data Breach Investigations Report, Verizon found that a data breach usually occurred within a matter of seconds or minutes after the attackers had successfully infiltrated a company’s computer systems. The attackers would then successfully begin exfiltrating the data only a few minutes thereafter. By contrast, Verizon found that detection would usually take at least a few weeks after the initial breach had occurred, giving the attackers plenty of time to do what they want with customers’ stolen data.
“Only 45% of survey respondents said they were confident in the secure configurations of their PoS devices.”
-Tripwire Online Survey, March 2015
Even then, for those that were in fact discovered, many of the breaches were not detected by the companies themselves. In fact, for 99% of the cases examined by Verizon, the affected companies were notified of the breaches by third parties—law enforcement entities or financial organizations following up on reports of payment card fraud, and in some cases customers who had been victimized in the incidents. Verizon also found that between 2011 and 2013, 45% of retail breaches occurred as a result of attackers exploiting the insecure configurations of company’s point-of-sale (PoS) devices. This is especially concerning given the fact that only half of our webcast’s attendees answered that they were confident in the secure configurations of their PoS devices. Clearly, computer criminals are interested in stealing customers’ payment card information, which helps to explain the uptick in breaches we are seeing today. This begs the question: How can we make sure a company does not succumb to large-scale payment card theft? The answer has to do with compliance. Information protection policies were created to ensure the protection of sensitive information. In this case, compliance with one such policy, known as the Payment Card Industry Data Security Standards (PCI DSS), helps to protect customers’ payment card information. To be sure, companies vary in their approach to the issue of compliance. Some organizations look at compliance as just a checkbox, implementing security controls in an effort to merely pass their security audit and thereby continue to do business. As I discussed in a recent post, however, this approach more often than not values a cheap solution to compliance at the expense of improving the organization’s security. It is therefore no surprise that many companies that implement the “checkbox” approach are predominantly those affected by large security breaches. Just to be clear, a comprehensive approach to compliance cannot prevent attackers from infiltrating a company’s networks. On the contrary, as the growing number of breaches has shown, it is inevitable that attackers will find a way in. But where PCI DSS compliance makes a difference is in a company’s detection and response time. Having the capabilities to quickly detect and remove an attacker from one’s network allows a company to resume business as usual in a matter of weeks. This is a preferred outcome when one considers the case of Target, which recently agreed to a multi-million dollar settlement after losing millions of customers’ data back in 2013. Today’s threat landscape necessitates that all companies strive to achieve continuous compliance with PCI DSS. If your organization is just embarking on this road, you can learn more, including some of the new requirements in PCI 3.0, by watching a full recording of our webcast here. Note: This article was co-authored by David Bisson and Irfahn Khimji.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

