
What is File Integrity Monitoring?
The IT ecosystems of enterprises are highly dynamic. Typically, organizations react to this volatility by investing in asset discovery and Security Configuration Management (SCM). These core controls enable businesses to compile an inventory of authorized devices and monitor the configurations of those assets. In addition to managing changes to their infrastructure, organizations must also keep an eye on the changes made to essential files. To overcome this issue, numerous businesses are implementing File Integrity Monitoring (FIM).
In 2001, when Visa was working on a security definition that would eventually become the Payment Card Industry Data Security Standard (PCI DSS) standard, the term "file integrity monitoring" was coined for the first time. This mention was in reference to the immensely popular Tripwire tool that led to Gene Kim founding the Tripwire company. Now, FIM, sometimes known as "change audit," is a component of virtually every IT compliance rule and standard as well as every IT security standard.
Integrity monitoring is used to detect and monitor modifications that may be suggestive of a cyberattack. File Integrity Monitoring entails explicitly examining files to see if and when they change, how they change, who altered them, and what can be done to restore them if unauthorized modifications occur. Companies can use this capability to monitor files for suspicious updates, such as hosts file entries, account permissions, software installation, or other indicators of compromise.
Consequently, FIM technology is functional for various use cases, but for the purposes of this blog, we will focus on ensuring compliance with frameworks and regulations such as PCI DSS.
What is the PCI DSS requirement?
PCI DSS 4.0 was released at the end of March, 2022, and Requirement 11.5.2 specifies that:
A change-detection mechanism (for example, file integrity monitoring tools) is deployed
as follows:
- To alert personnel to unauthorized modification (including changes, additions,
and deletions) of critical files. - To perform critical file comparisons at least once weekly.
The Standard explains that “critical files are usually those that do not regularly change, but the modification of which could indicate a system compromise or risk of compromise.” Changes to critical system, configuration, or content files can be an indicator that an attacker has accessed an organization’s system. Such changes can allow an attacker to take additional malicious actions, access cardholder data, and/or conduct activities without detection or record.
How FIM ensures compliance with PCI DSS 4.0
All banking institutions need to be compliant with PCI DSS Requirement 11, otherwise sensitive financial data, such as cardholder or account data, can be compromised and critical operations might halt. The impact of such incidents is enormous, both for customers as well as for the victim company.
Hence, these organizations employ FIM tools to identify whether a detected change is authorized or not and help to determine potential suspicious activity. Although change management could be performed manually, this is definitely not a best practice, especially considering the vast amount of critical data a financial organization stores and the herculean effort required to accomplish this
The Tripwire Enterprise FIM solution automates file monitoring, enabling financial and banking organizations to save significant time and effort. This is where the real added value of our FIM solution arises – reduce the noise of false positive alerts, provide accurate findings to ensure that file integrity is always preserved with time-savings and efficiency, and minimize human error in the process.
Another benefit often reported by financial institutions is that FIM solutions allow for smoother and quicker audits. When a Qualified Security Assessor (QSA) visits an organization, the inspected company needs to provide evidence that they are implementing change management per the PCI DSS requirement. The reporting provided from the Tripwire Enterprise FIM solution speeds up the process and makes the audit go smoother, avoiding any additional questions about how the information was extracted. Tripwire Enterprise has been a leader in this effort for many years, so most auditors are familiar with the solution.
Finally, a FIM solution becomes a handy tool when it has the capacity to integrate with a wide variety of operating systems and devices. As the businesses technology stack includes diverse systems and network devices, it makes perfect sense to be able to monitor and record changes across the enterprise ecosystem. Having an out-of-the-box coverage of the business environment ensures that all critical files and systems are monitored to prevent any unauthorized modification that could jeopardize the integrity and confidentiality of financial data.
Ensure PCI DSS compliance with Tripwire FIM
Tripwire Enterprise File Integrity Monitoring solution focuses on giving business context to data for your critical environment-related changes within an enterprise. As a result, it provides IT and security teams with real-time intelligence that may be used to identify situations of genuine concern. It also assists workers in gaining knowledge about the who, what, when, and how of a change, which they can use to validate proposed alterations.
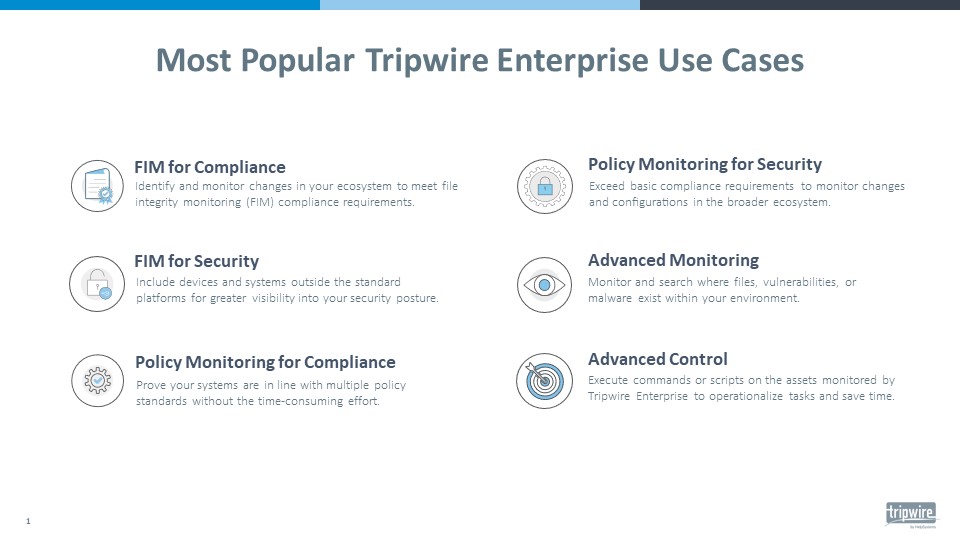
If you want to discover more use cases of Tripwire FIM solution you can download this handy guide.
