
Phishers leveraged fake automated messages from collaborative platform Sharepoint as a means to target users' Office 365 credentials. Abnormal Security found that the phishing campaign began with an attack email that appeared to be an automated message from Sharepoint. To add legitimacy to this ruse, the attackers used spoofing techniques to disguise the sender as Sharepoint. They also didn't address the email to a single employee but included multiple mentions of the targeted company.
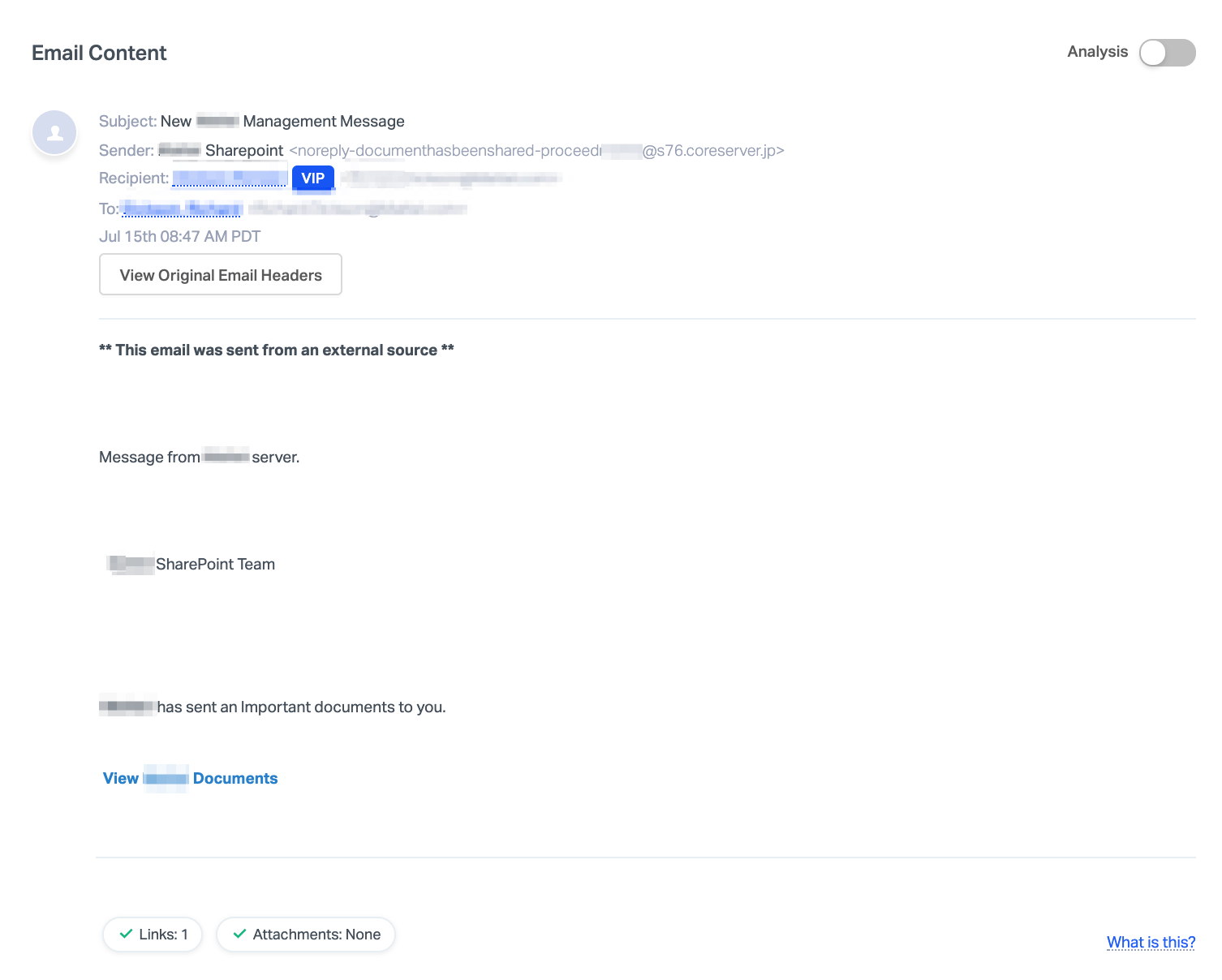
Screenshot of attack email (Source: Abnormal Security) The malicious actors used those tactics in the hope that at least one employee would fall for the phish and click on the "View xx Documents" hyperlink. Once clicked, that link used a series of redirects to send the recipient to a landing page disguised to look like a secure Sharepoint file. It also employed Sharepoint and Microsoft branding to convince the user that it was safe to submit their credentials in order to view the file. Alternatively, the landing page prompted the user to download a PDF document that then redirected them to another malicious site. Abnormal Security put the risks of this campaign into context:
If the recipient falls victim to this type of attack, their credentials are compromised, as well as any data stored on their account. This places employees and their networks at considerable risk as attackers can launch internal attacks to steal more credentials and information from the organization.
This wasn't the first time that Sharepoint played some role in nefarious individuals' efforts. Back in September 2019, for instance, security researchers spotted a phishing campaign that used SharePoint to bypass email gateway and other perimeter technologies. It was less than a year later when security analysts found that attackers were using fake emails from Sharepoint as well as exploiting the fact that email gateways turn a blind eye to links to popular sites such as YouTube in order to phish passwords. These attack attempts highlight the need for organizations to defend themselves against a phishing attack. They can do so by educating their users about some of the most common types of phishing campaigns in circulation today.

