Why leveraging live environment simulations and putting ICS tools to the test is the best way to evaluate their fitness. Track and field was one of my favorite sports growing up. I didn’t begin competitively participating until I was a teenager, but I was instantly hooked once I started. Why? Because the clock didn’t lie. The tape measure didn’t lie. The fastest time always won, and the longest throw always won. I like to think of ICS security tools in a similar way. When determining what tool is best for your environment, you need to see them live as they’re playing the game. Marketing spin and the universal statement of “our ICS tool is the best out there” needs to be equally met by strong performance. So as you’re looking to evaluate and navigate through messages from dozens of providers, make it a competition to your benefit. [embed]https://youtu.be/eJg5qfFHRIk[/embed] Some ways in which you can gamify ICS security solution evaluation:
Ask for a demonstration with your environment’s data.
All of us vendors have figured out how to show you our best demo. If you leave it up to us, we’re going to load up the ideal scenarios that highlight the best features of our tools. While this is certainly beneficial information for you, it can be made even richer if you ask a vendor to consume some of your own network’s traffic (by sending over a packet capture or doing a live proof of concept) to see how the tool performs. That way, you get a preview of what interaction with the tool would be like for your specific use cases.
Ask to see the whole portfolio.
Most users today are looking for asset visibility and anomaly detection applications that have a combination of passive and active data collection methods. That’s a great place to start! But as we at the State of Security have long and often communicated, cybersecurity is a process, not a project. If you only look at which vendors have asset visibility platforms today but don’t probe their cybersecurity vision, you could find yourself needing to pivot to a new vendor in the future so that you can receive broader coverage from a greater spectrum of security controls as your needs evolve.
Ask what kinds of tools and research each vendor uses to support new developments and vulnerability support.
Our industry needs to continually adapt with the threat landscape. This includes continuously developing new features and methodologies to stay ahead of the attacks and also speedy responses to newly published vulnerabilities. Is the vendor you’re considering a leader or a follower here?
One of the steps Tripwire has taken to remain focused and proactive in the space is the launch of our new ICS lab in the Silicon Valley, California. We have been acquiring and adding new devices from common vendors like Schneider Electric, Rockwell Automation, ABB, Siemens and Schweitzer Engineering Laboratories in addition to incorporating our own Hirschmann, GarrettCom, Tofino, and ProSoft gear to best simulate a variety of ICS environments.
We’re proud to have opened this lab in Q4 of last year, and we’re already using the space for a variety of purposes:
-
- Our developers are able to use real data to improve the use of existing Tripwire products and build new solutions.
- Our systems engineers are able to demonstrate real system data and how Tripwire controls interact with it.
- Users can visit us live at our lab to see interactive demos of our solutions.
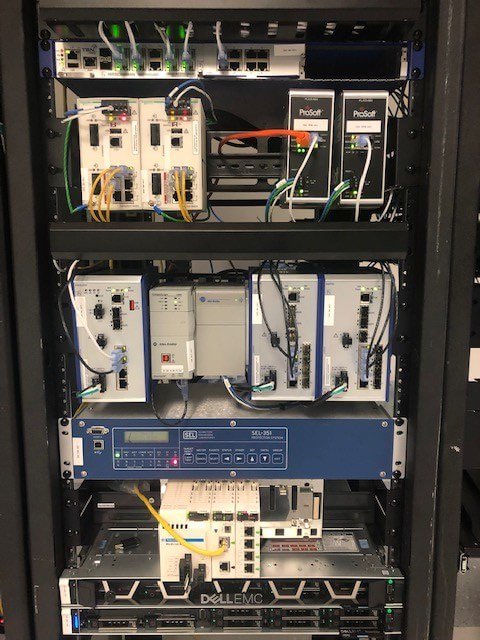
We plan to continually expand the lab throughout 2020 to add more devices in all layers of the environment, all the way down to field-level IO. For more information on our lab or on Tripwire’s solutions for industrial environments, please click here.

