
Security researchers have released a tool that enables victims of GetCrypt ransomware to recover their affected files for free. On 23 May, web security and antivirus software provider Emsisoft announced the release of its GetCrypt decrypter. This utility asks victims of the ransomware to supply both an encrypted copy and the original version of a single file. It also asks that they include a copy of the ransom note. Emsisoft explains that this threatening message, named "# DECRYPT MY FILES #.txt," usually goes something like this:
Attention! Your computer has been attacked by virus-encoder! All your files are now encrypted using cryptographycalli strong aslgorithm. Without the original key recovery is impossible. TO GET YOUR DECODER AND THE ORIGINAL KEY TO DECRYPT YOUR FILES YOU NEED TO EMAIL US AT: [email protected] It is in your interest to respond as soon as possible to ensure the restoration of your files. P.S only in case you do not recive a response from the first email address within 48 hours, [redacted]
The tool will then use those resources together to reverse GetCrypt's encryption process and begin decrypting victims' files.
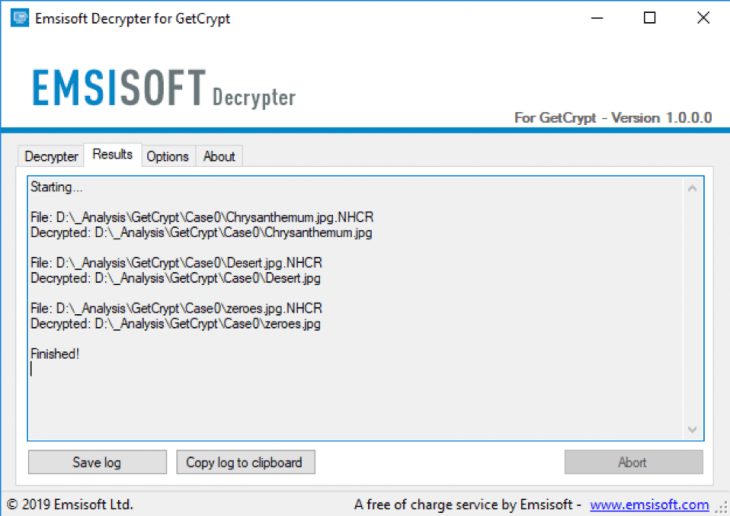
Successful Emsisoft GetCrypt Decryption. (Source: Emsisoft) Discovered by exploit kit researcher nao_sec, an GetCrypt infection begins when the Popcash malvertising campaign redirects Windows users to a page hosting the RIG exploit kit. This software package has been involved in numerous attack campaigns and has helped spread various digital threats in the process over the past few years. In this particular operation, malicious scripts included in the RIG exploit kit try to abuse known vulnerabilities so that it can install GetCrypt. As reported by Bleeping Computer, the executed ransomware checks to see if the computer's language is Ukrainian, Belarusian, Russian or Kazakh. If it is, it terminates and doesn't encrypt anything. If it is not, it refers to the CPUID of the computer and uses it to create a four-character string which it eventually appends to the name of each file it encrypts. During the encryption process, the threat also attempts to enumerate a list of network file shares. If this proves unsuccessful, it moves on to bruteforce the credentials for available shares using a list of hardcoded usernames and passwords. GetCrypt underscores the point that ransomware remains a relevant force in today's digital threat landscape. Organizations and users should respond by backing up their critical data on a regular basis and making sure their software is up-to-date. They should also follow these additional prevention tips designed to prevent a ransomware infection.

