
In February 2016, Tripwire first unveiled the results of its 2016 Breach Detection Survey. The study polled the comments of 763 security information security personnel about their organizations' efficacy of implementing seven key security controls: PCI DSS, SOX, NERC CIP, MAS TRM, NIST 800-53 and IRS 1075. Those controls are essential to helping an organization detect a digital attack in a timely manner. Tripwire has learned many things from its survey, but if one lesson stands out, it's that most IT professionals are overconfident about their ability to detect a security incident. For instance, Dimensional Research, which acted on behalf of Tripwire in conducting the survey, found that at least 60 percent of respondents were unsure how long it would take for their organization's automated tools and vulnerability scanning systems to pick up on an unauthorized configuration change or generate an alert. But when asked how long they thought those processes would take, an even greater percentage of participants said minutes or hours. Those responses in no way cohere with Verizon's 2015 Data Breach Investigations Report, which found breach detection on average takes several months. To understand the extent to which overconfidence permeates the security industry, Tripwire broke down its survey by sector and analyzed the responses. It observed an equal, if not higher rate, of overconfidence among IT professionals working in the financial, federal government and energy industries. After separating out the responses of 100 personnel in the retail industry, Tripwire can now say breach detection overconfidence is an overarching force in the security community.
"There's Still a Lot of Room for Improvement"
Although bad actors continue to target retailers, IT professionals working in that sector are overconfident about their organization's ability to quickly detect and respond to a breach. What it comes down to is a discrepancy in belief versus knowledge. Here are some statistics to illustrate that point:
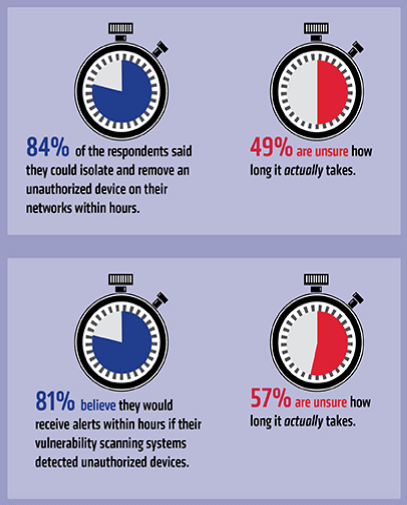
- 79 percent of infosec personnel think they could detect configuration changes to their organization's endpoint devices within a matter of hours, but approximately half (49 percent) don't know how long that process actually takes.
- A majority of IT professionals said they're unsure how long it would take for their vulnerability scanning systems to generate an alert after detecting unauthorized devices on their organization's network. In reality, more than four-fifths (81 percent) of IT professionals still believe that process would take only hours.
- In just a few hours, nearly all (89 percent) of respondents think they could remove an unauthorized device from their organization's network, though just about half (49 percent) don't know if they actually could in that short amount of time.
Tim Erlin, senior director of IT security and risk strategy at Tripwire, feels that those perceptions illustrate how organizations still have work to do to improve their breach detection capabilities:
"The increased scrutiny of retail cyber security in the wake of major breaches has forced organizations to focus on securing their environments, yet these survey results show that there's still a lot of room for improvement."
Perception isn't the sole source of the problem, either.
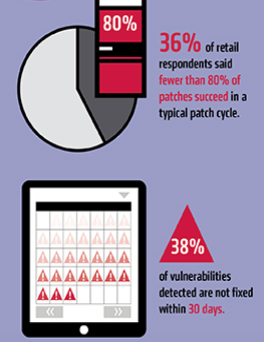
Dimensional Research found that about half (36 percent) of respondents said fewer than 80 percent of patches succeed in a typical patch cycle. Additionally, about that same percentage of respondents (38 percent) stated detected vulnerabilities are not fixed within the first 30 days.
Conclusion
Given those security oversights identified in Tripwire's survey, Erlin recommends that organizations in the retail sector emphasize security controls at the workplace: "Retailers are well aware of the risks involved and need to remain focused on implementing strong controls to limit malicious access to their environments." For insight into how retailers can defend against some of the most pressing security challenges, please read The State of Security's coverage of the 2016 Retail Cyber Intelligence Summit.
