
Every year, the Verizon Data Breach Investigations Report comes out, and there’s a mad scramble to inspect and interpret the data. The report is data-rich, as always, and already contains a bunch of analysis, so there are really only a few options for adding value to the conversation. Industry commentators can choose to disagree with the analysis, expand on some part of the data or pull out specific points to emphasize. I always find specific value in the more detailed analysis by sector. The overall themes and trends don’t tend to vary so much, but the industry detail is more actionable. First, it may seem obvious, but it’s important to understand the distinction between incidents and breaches in the DBIR. There are a fair number of pretty charts and graphs in here, but they mean very different things depending on which of these two categories they apply to. Incidents include just about anything reported regardless of whether data was confirmed to be compromised. Breaches, on the other hand, are only those incidents in which data was actually compromised. My bias is to look at the breach data because incidents are a dime-a-dozen whereas breaches are where the rubber meets the road. For an overview that includes an industry sector perspective, my favorite section of the DBIR is this set of matrices in ‘Victim Demographics and Industry Analysis.’
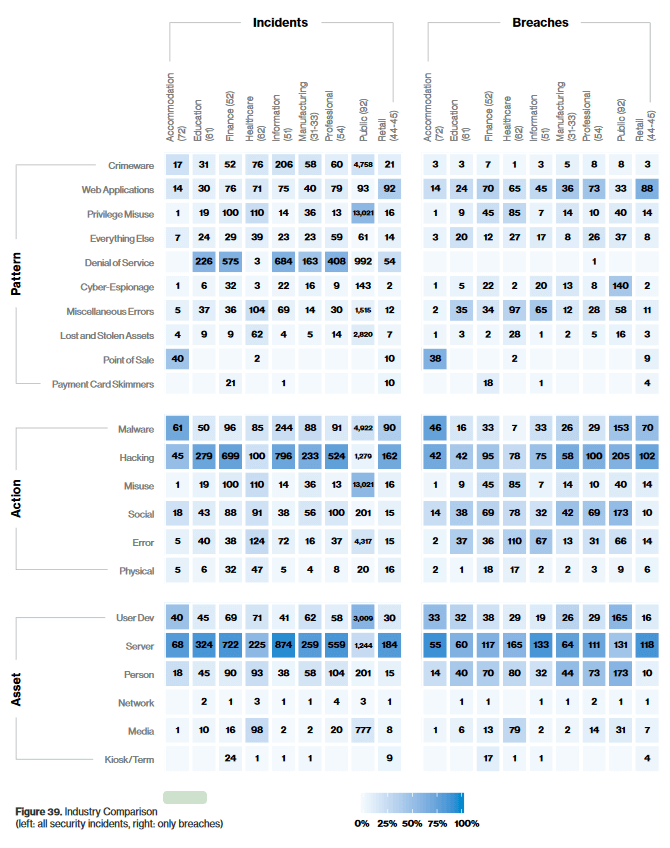
This visual representation provides you with the ability to quickly identify outliers and problem areas in ways that are meaningful. For example, you can see plainly that ‘hacking’ is an action that broadly impacts the industry sectors across both incidents and breaches. As a target, servers are also, broadly, the assets most impacted. You also might notice the significant contrast between incidents and breaches around the pattern of denial of service. Very simply, DoS is the primary pattern for the majority of incidents but not breaches. You also see commonality across the two with ‘hacking’ and ‘servers.’ These are examples where the attributes of incidents and breaches are similar. In other words, investment in protecting against hacking and securing your servers will likely bring down both incidents and breaches, but DoS protections will have little impact on breaches. Of course, the real value in this view is around the specific industry sectors. For example, if you’re in retail, you should definitely pay attention to how you secure your web applications, how you protect against hacking and how you secure your servers. It wouldn’t be bad to have a strategy for malware protection, too. If you’re in the public sector, you should be more concerned with cyber-espionage, hacking and maybe people a little more than servers. You can see that the conclusions are substantially different when comparing retail and public sectors. It may seem intuitive that retail doesn’t have to worry about cyber-espionage as much, but the emphasis on people as targeted assets for the public sector could make a big difference in how budget is applied. Healthcare has the most problems with miscellaneous errors, a departure from most other sectors. Privilege misuse, which you could see as related, isn’t far behind either. The actions for healthcare cluster in an interesting way, with the top three being hacking, social engineering and misuse. When you look at healthcare as a whole, you might draw some useful conclusions about how budget should be applied, specifically to technology and process around data access. As you might have noted, this type of sector-specific analysis is invaluable in budget conversations. There’s more of this detail in the individual sections dedicated to each sector. It’s worth reading if you have a specific interest. This particular view might drive some of that interest, as well. As I said at the start, there’s a ton of useful data and analysis in the DBIR. It’s important to keep in mind what you’re trying to accomplish in dissecting it. A goal-oriented reading is a good strategy. To read the full DBIR report, click here.

