
The healthcare industry is no stranger to data breaches. In 2017, SSM Health, the University of Iowa Health Care (UIHC), and Arkansas Oral & Facial Surgery Center all suffered security incidents where bad actors possibly exposed patients' medical data. No doubt there are also countless other healthcare organizations that have yet to detect an ongoing system compromise. Notwithstanding these events, most healthcare IT professionals feel confident they can detect and remediate a breach. Ninety percent of participants in a 2016 Tripwire study believed it would take their employer's vulnerability scanning systems just hours to generate an alert if an unauthorized device connected to the network. Yet 49 percent of respondents admitted they had no idea how long that process would take. Healthcare IT professionals responded similarly with respect to configuration changes. Eighty-four percent thought they could detect such modifications to a network device within hours. At the same time, 54 percent didn't know the average timing of detection. IT personnel working in healthcare might very well be placing too much faith in their organization's breach preparedness. By no means, however, are they the only ones to feel overconfident about their employer's ability to detect a security incident. A survey conducted by the University of Phoenix reveals healthcare professionals are also overoptimistic. Between August 15 and September 1, 2017, the University of Phoenix commissioned Harris Poll to survey 504 adults working in the United States either as registered nurses (RNs) or as administrative staff. When asked if they felt "very confident" in their organization's ability to secure patient data against potential theft, 48 percent of RNs answered affirmatively. A slightly higher percentage of administrative staff (57 percent) expressed a similar sentiment.
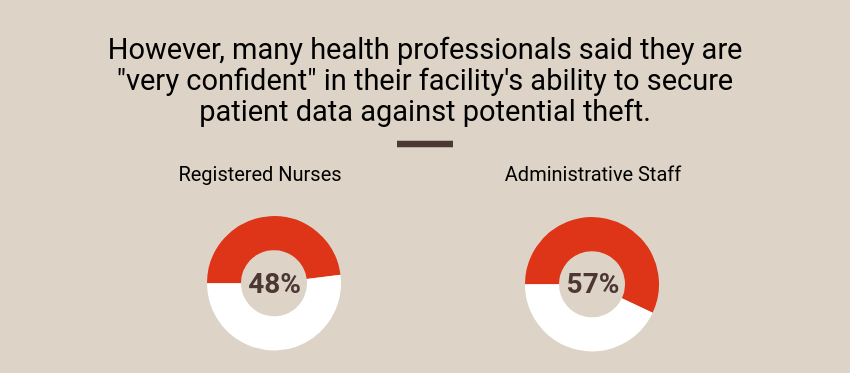
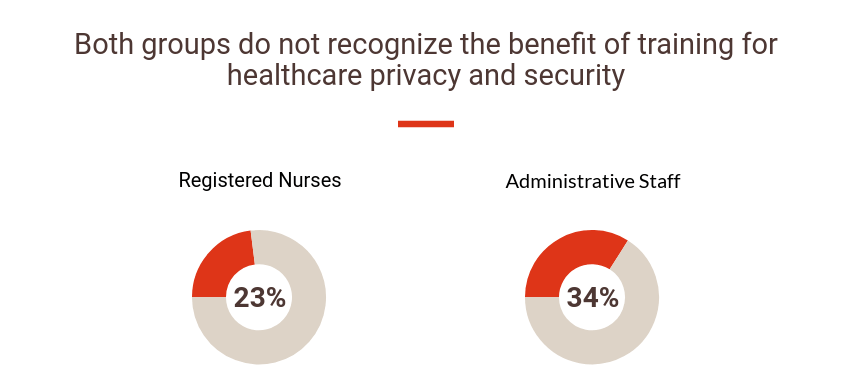
Source: The University of Phoenix That being said, they might not have reason to feel that way. Twenty-one percent of RNs who participated in the University of Phoenix survey said they didn't know if their company had suffered a breach of patient data in the past year. Even more than that (25 percent) didn't know if their employer had changed how they handle data security and patient privacy in the past year. Assuming those security policy modifications had not occurred, respondents didn't agree on what those changes should be. Nearly half of administrative staff and two in five RNs said more technology training was needed. Even so, percentages of both groups admitted they didn't see the benefit of such training (23 percent of RNs and 34 percent of administrative staff).
Source: The University of Phoenix Fortunately, healthcare organizations aren't taking the threat of a data breach sitting down. The University of Phoenix's survey reveals that healthcare organizations are defending against security incidents by investing in controls, such as updated privacy and access policies (69 percent of admin staff and 67 percent of RNs), role-based access (60 percent of admin staff and 59 percent of RNs), and data surveillance (55 percent of admin staff and 56 percent of RNs). They are also turning to other methods, such as security risk assessments and single sign on services. Such investment is encouraging. All healthcare organizations face the real threat of a data breach, so they need to make a concerted effort to harden the security of their systems. For information on how Tripwire's solutions can help in this regard, click here. You can also read more findings from the University of Phoenix's survey here.

