
For the first time on record, the Department of Homeland Security (DHS) and the Federal Bureau of Investigation (FBI) publicly blamed Russia for attempting to hack U.S. energy infrastructure. On 15 March, DHS and FBI published a joint Technical Alert (TA) via the United States Computer Emergency Readiness Team (US-CERT). In it, officials say Russian government digital actors are targeting American energy organizations along with government entities and other critical infrastructure sectors. As revealed by the TA, Russia is approaching its hacking attacks against U.S. targets in stages:
This campaign comprises two distinct categories of victims: staging and intended targets. The initial victims are peripheral organizations such as trusted third-party suppliers with less secure networks, referred to as “staging targets” throughout this alert. The threat actors used the staging targets’ networks as pivot points and malware repositories when targeting their final intended victims. NCCIC and FBI judge the ultimate objective of the actors is to compromise organizational networks, also referred to as the “intended target.”
The campaigns begin with Russian actors conducting reconnaissance of staging targets that at some point maintained relationships with their intended targets. Using the information they acquire, the individuals launch spear-phishing attacks against the staging targets, compromise their web-based infrastructure with malicious content, and develop watering holes to infect their intended target. Once inside their intended target's network, they create web shells on the entity's email and web servers and conduct reconnaissance against ICS and supervisory control and data acquisition (SCADA) systems.
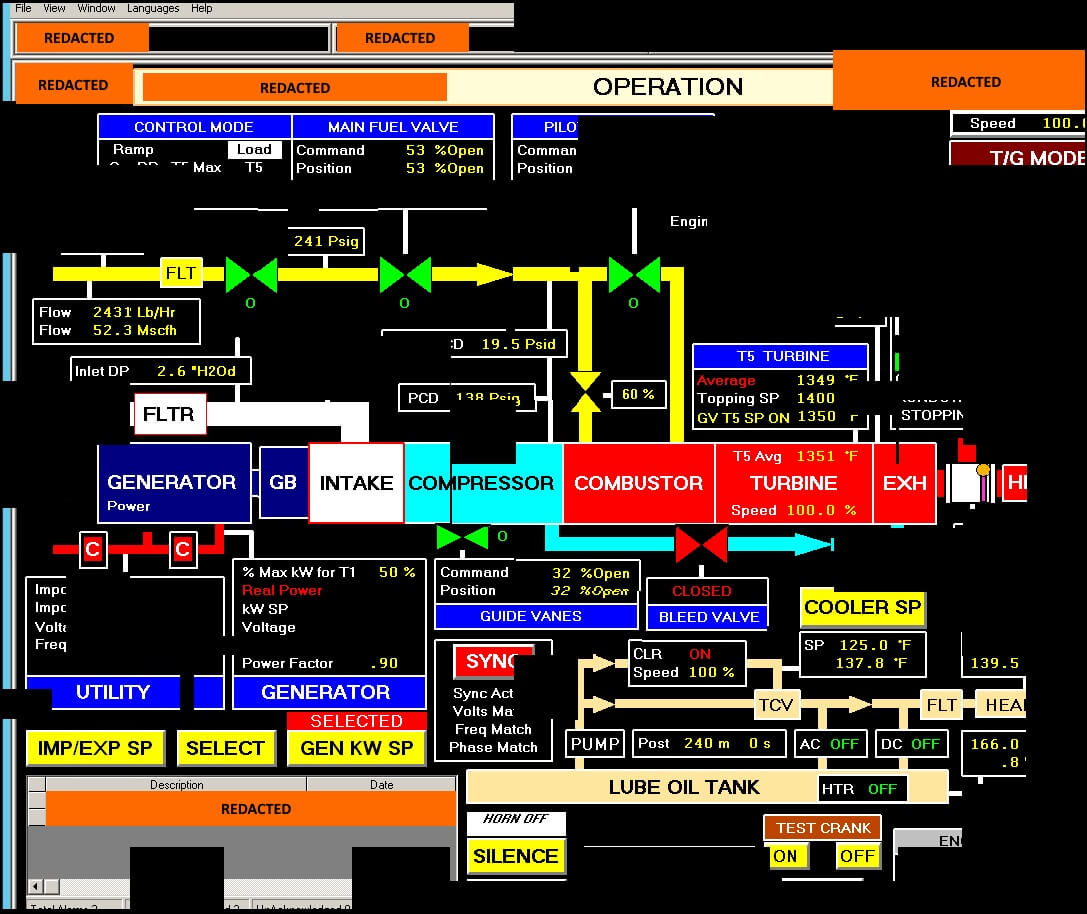
Reconstructed screenshot fragments of a Human Machine Interface (HMI) that the threat actors accessed. (Source: US-CERT) Russian black-hat hackers then create other accounts inside the intended target's network to help remove signs of the intrusion. Amit Yoran, a former U.S. official who founded US-CERT, told The New York Times that the decision of the U.S. government to publicly attribute these attacks to Russia is "unprecedented and extraordinary," saying he's never seen anything like it. The TA appears to provide details about Dragonfly 2.0, a threat actor detected by Symantec which has targeted energy organizations in the United States, Turkey, and Switzerland with malicious email campaigns since at least 2015. The security firm's original report on Dragonfly 2.0 doesn't mention Russia as a possible culprit for the attacks. In response to attempts to penetrate the American energy grid and meddle in the 2016 U.S. presidential election, the Trump Administration imposed new sanctions against Russian organizations and individuals on the same day as the TA's release. Treasury Secretary Steven Mnuchin said in a statement that the sanctions are justified:
The administration is confronting and countering malign Russian cyberactivity, including their attempted interference in U.S. elections, destructive cyberattacks and intrusions targeting critical infrastructure. These targeted sanctions are a part of a broader effort to address the ongoing nefarious attacks emanating from Russia.
Moscow has denied involvement in the hacking attacks, with Sergei Ryabkov, a deputy foreign minister for Russia, saying that the new sanctions are "purely tied to the internal American infighting." DHS and FBI issued their TA at a time when attacks against energy organizations are ramping up around the world. These include efforts by APT33 to target Saudi petrochemical entities and other energy organizations with spear-phishing campaigns. Given the rise in these attacks, it's important that organizations invest in a solution that can help them monitor their ICS and SCADA systems for potentially malicious behavior. For information on how Tripwire can help, click here.
Achieving Resilience with NERC CIP
Explore the critical role of cybersecurity in protecting national Bulk Electric Systems. Tripwire's NERC CIP Solution Suite offers advanced tools for continuous monitoring and automation solutions, ensuring compliance with evolving standards and enhancing overall security resilience.

