
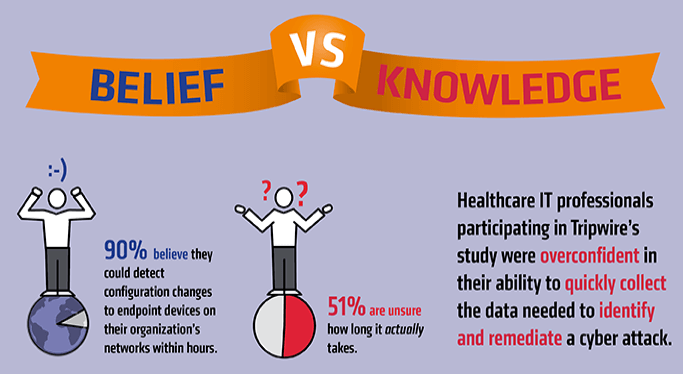
IT professionals are instrumental to strengthening an organization's digital security. They must fulfill a variety of duties to work towards that end. One of their most important responsibilities is helping their company detect and respond to data breaches. But there's a problem. Most information security personnel are overconfident in their organization's breach prevention and response capabilities. That perception isn't unique to one sector, either. It reaches across every industry. Such is what Tripwire observed in its 2016 Breach Detection Survey. Conducted by Dimensional Research, the study evaluated the confidence and efficacy with which 763 IT professionals in the United States implement security controls required by PCI DSS and other compliance regulations. Those measures include comprehensive vulnerability management, log management, and several other processes as parts of an ongoing endpoint security strategy. Most survey respondents working in finance, federal government, energy, and retail revealed they hold historically unrealistic expectations when it comes to their organization's breach detection and response strategies. After once again breaking down its study's findings, Tripwire now knows those in the healthcare sector feel the same way. Indeed, most healthcare IT professionals interviewed by Dimensional Research for Tripwire's study were overconfident in their ability to quickly detect and remediate a breach. For instance, while almost all (90 percent) of respondents said it would take them just hours to detect configuration changes to their organization's endpoint devices, more than half (51 percent) admitted they had no idea how long that process would take.
Tim Erlin, senior director of IT security and risk strategy at Tripwire, attributes this discrepancy to a lack of basic security controls:
"There's no argument that these basic controls work and contribute directly to an organization's cyber security, yet the research shows they are not in place at enough health care organizations. This is occurring at a time when the health care industry is facing unique cyber threats, from physical theft to sophisticated ransomware campaigns."
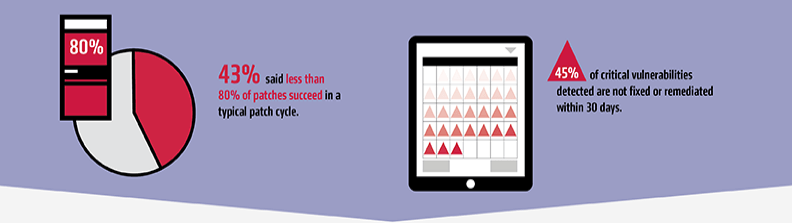
Tripwire verified in its survey that healthcare organizations are struggling to implement basic controls. Overall, 60 percent of respondents said they don't believe automated tools pick up all the information needed to pinpoint the location of an unauthorized network device. That's assuming they detect the unsanctioned device in the first place. Organizations' records of patch management aren't much better. 43 percent of IT professionals said less than 80 percent of all fixes succeed on a typical patching cycle. It's therefore not a surprise that nearly half (45 percent) of all known vulnerabilities aren't remediated or fixed within 30 days.
Erlin feels such security lapses are unacceptable:
"The basics of finding unauthorized devices and vulnerabilities and applying patches in a timely manner should be done at every organization in order to create a baseline of cyber security. These fundamental controls should be in place before organizations look at the latest shiny security object."
Fortunately, healthcare organizations can implement basic controls by first learning more about endpoint detection and response (EDR). EDR is a process that among other things requires security personnel to keep an inventory of hardware and software as well as stay aware of vulnerabilities that threaten network assets. As a result, IT professionals can use EDR to overcome their overconfidence and strengthen the security posture of their organization.

